2023
Yanjie Zhang, Bilal Ayyub, Wenping Gong, Huiming Tang
Landslides frequently disrupt roadway networks in mountainous regions worldwide. Because of the relatively long roadway extension and low roadway density in mountainous regions, the occurrence of a landslide hazard along a local road segment will cause traffic paralysis on the individual roadway and will further impact regional roadway network accessibility. This paper establishes an integrative risk assessment framework based on risk theory and complex network theory to combine the results of landslide susceptibility mapping along roadways and impact assessment on the roadway network. Through an analysis of the relationship between various geo-environmental conditioning factors and historical landslides along roadways, the support vector machine (SVM) model is used to assess landslide susceptibility across the regional roadway network.
Landslides
2023
Panagiotis Nikolaidis, Asim Zoulkarni, John Baras
The authors develop a Bandwidth Demand Estimator (BDE); a network function that periodically monitors the traffic of a Network Slice (NS) and adapts the bandwidth at the base station to efficiently meet its packet delay requirements.
arXiv.org
Nariman Torkzaban, Mohammad Khojastepour, John Baras
Distributed massive MIMO networks are envisioned to realize cooperative multi-point transmission in next-generation wireless systems. For efficient cooperative hybrid beamforming, the cluster of access points (APs) needs to obtain precise estimates of the uplink channel to perform reliable downlink precoding. However, due to the radio frequency (RF) impairments between the transceivers at the two en-points of the wireless channel, full channel reciprocity does not hold which results in performance degradation in the cooperative hybrid beamforming (CHBF) unless a suitable reciprocity calibration mechanism is in place. This paper proposes a two-step approach to calibrate any two hybrid nodes in the distributed MIMO system. We then present and utilize the novel concept of reciprocal tandem to propose a low-complexity approach for jointly calibrating the cluster of APs and estimating the downlink channel.
arXiv.org
Nariman Torkzaban, Mohammad Khojastepour, John Baras
This paper proposes a low-overhead blind CFO estimation technique based on cyclic prefix (CP), in multi-input multi-output (MIMO)-OFDM systems. Antenna diversity is used for CFO estimation.
arXiv.org
Nariman Torkzaban, Asim Zoulkarni, Anousheh Gholami, John Baras
Non-geostationary (NGSO) satellite communications systems have attracted a lot of attention both from industry and academia, over the past several years. Beam placement is among the major resource allocation problems in multi-beam NGSO systems. In this paper, the authors formulate the beam placement problem as a Euclidean disk cover optimization model. They aim at minimizing the number of placed beams while satisfying the total downlink traffic demand of targeted ground terminals without exceeding the capacity of the placed beams.
arXiv.org
Nariman Torkzaban, Mohammad A. Amir Khojastepour, John Baras
Reciprocity mismatch deteriorates the performance of mm-Wave hybrid beam-forming and has to be estimated and compensated for, to avoid performance degradation in the co-operative hybrid beamforming. In this paper, the researchers address the channel reciprocity calibration between any two nodes at two levels.
2023 IEEE Wireless Communications and Networking Conference (WCNC)
Christos N. Mavridis, Aris Kanellopoulos, Kyriakos G. Vamvoudakis, John Baras, Karl Henrik Johansson
Addresses the problem of identifying the cognitive ability level of agents attacking a cyber-physical system.
KTH website paper
Anousheh Gholami, Nariman Torkzaban, John Baras
Proposes a practical two-time-scale resource provisioning framework for E2E network slicing under demand uncertainty.
arXiv.org
Nariman Torkzaban, Mohammad Amir Khojastepour, Mohammad Farajzadeh-Tehrani, John Baras
The next generation of wireless communication systems aims to address the ever‑increasing demand for high throughput, low latency, better quality of service, and ubiquitous coverage. While the abundance of bandwidth available at the mmWave frequency range is considered a key to realizing next-generation wireless promises, mmWave suffers from high path loss and poor scattering and diffraction, and is vulnerable to shadowing, blockages and blind spots, especially in urban areas. This paper introduces the concept of “multi‑beamforming,” to address the design of beams consisting of multiple disjoint lobes to cover different blind spots using sharp, high gain, and effective beam patterns.
ITU Journal on Future and Evolving Technologies (ITU J-FET) special issue on Intelligent surfaces and their applications towards wide-scale deployment Best paper award
Panagiotis Nikolaidis, Asim Zoulkarni, John Baras
Considers the tradeoff between resource efficiency and performance isolation that emerges when multiplexing the resource demands of Network Slices (NSs). The analysis of this tradeoff enables network operators to determine the effect of performance isolation on the operating cost of each NS.
arXiv.org
Nariman Torkzaban, Asim Zoulkarni, Anousheh Gholami, John Baras
Non-geostationary (NGSO) satellite communications systems have attracted a lot of attention both from industry and academia over the past several years. Beam placement is among the major resource allocation problems in multi-beam NGSO systems. In this paper, the authors formulate the beam placement problem as a Euclidean disk cover optimization model. They aim at minimizing the number of placed beams while satisfying the total downlink traffic demand of targeted ground terminals without exceeding the capacity of the placed beams. They present a low- complexity deterministic annealing (DA)-based algorithm to solve the NP-hard optimization model for near-optimal solutions.
arXiv.org
2022
Faizan M. Tariq, Nilesh Suriyarachchi, Christos Mavridis, John Baras
Safe overtaking, especially in a bidirectional mixed-traffic setting, remains a key challenge for Connected Autonomous Vehicles (CAVs). The presence of human-driven vehicles (HDVs), behavior unpredictability, and blind spots resulting from sensor occlusion make this a challenging control problem. To overcome these difficulties, the authors propose a cooperative communication-based approach that utilizes the information shared between CAVs to reduce the effects of sensor occlusion while benefiting from the local velocity prediction based on past tracking data.
2022 IEEE 25th International Conference on Intelligent Transportation Systems (ITSC)
Panagiotis I. Nikolaidis, John Baras
Proposes an online resource allocation scheme for end-to-end network slices. The scheme is based on an optimization problem, where bandwidth allocation is jointly performed in the radio access network, and service function chain is embedded in the core network. The scheme has polynomial time complexity and is fast and highly scalable with respect to the number of users.
2021 IEEE Global Communications Conference (GLOBECOM)
Erfaun Noorani, Yagiz Savas, Alec Koppel, John Baras, Ufuk Topcu, Brian M. Sadler
Considers a group of agents that estimate their locations in an environment through sensor measurements and aim to transmit a message signal to a client via collaborative beamforming.
2021 55th Asilomar Conference on Signals, Systems, and Computers
Nariman Torkzaban, Mohammad Amir Khojastepour, John Baras
To overcome high path loss and the intense shadowing in millimeter-wave (mmWave) communications, effective beamforming schemes are required which incorporate narrow beams with high beamforming gains. The mmWave channel consists of a few spatial clusters each associated with an angle of departure (AoD). The narrow beams must be aligned with the channel AoDs to increase the beamforming gain. This is achieved through a procedure called beam alignment (BA). The authors propose efficient BA schemes in presence of multipath.
arXiv.org
2021
Dipankar Maity, David Hartman, John Baras
The authors consider the classical sensor scheduling problem for linear systems where only one sensor is activated at each time. They show that the sensor scheduling problem has a close relation to the sensor design problem and the solution of a sensor schedule problem can be extracted from an equivalent sensor design problem. They also propose a convex relaxation to the sensor design problem and a reference covariance trajectory is obtained from solving the relaxed sensor design problem.
arXiv.org
Nariman Torkzaban, John Baras
SDN-enabled Integrated satellite-terrestrial networks (ISTNs), can provide several advantages including global seamless coverage, high reliability, low latency, etc. and can be a key enabler towards next generation networks. To deal with the complexity of the control and management of the integrated network, leveraging the concept of software-defined networking (SDN) will be helpful. In this regard, the SDN controller placement problem in SDN-enabled ISTNs becomes of paramount importance. The authors formulate an optimization problem for the SDN controller placement with the objective of minimizing the average failure probability of SDN control paths to ensure the SDN switches receive the instructions in the most reliable fashion.
arXiv.org
Anousheh Gholami, Nariman Torkzaban, John Baras
The paper proposes trust as a measure to evaluate the status of network agents and improve the decision making process. The authors interpret trust as a relation among entities that participate in various protocols.
arXiv.org
Touraj Soleymani, John Baras, Sandra Hirche, Karl Johansson
The rate-regulation trade-off defined between two objective functions, one penalizing the packet rate and the other, the state deviation and control effort, can express the performance bound of a networked control system. However, the characterization of the set of globally optimal solutions in this trade-off for multi-dimensional controlled Gauss-Markov processes has been an open problem. In the present article, we characterize a policy profile that belongs to this set. We prove that such a policy profile consists of a symmetric threshold triggering policy, which can be expressed in terms of the value of information, and a certainty-equivalent control policy, which uses a conditional expectation with linear dynamics.
arXiv.org
Nariman Torkzaban, John Baras
Several challenging optimization problems arise while considering the deployment of the space-air-ground integrated networks (SAGINs), among which the optimal satellite gateway deployment problem is of significant importance. Moreover, with the increasing interest in the software-defined integration of 5G networks and satellites, the existence of an effective scheme for optimal placement of SDN controllers, is essential. The authors discuss the interrelation between the two problems above and propose suitable methods to solve them under various network design criteria.
arXiv.org
Siyi Wang, Qingchen Liu, Precious Ugo Abara, John Baras, Sandra Hirche
The authors address the trade-off between control performance and communication cost for a multi-loop NCS. They analytically characterize the relationship between quality of control and VoI function. The derived VoI functions properly reflect the relevance of information including temporal aspects for the control task and are parameterized by the coupling variables such as delay induced by the network. The data packet is transmitted through the network whenever the value of information is positive to preserve the control tasks. Finally, the numerical simulation is provided to verify the effectiveness of the VoI-based scheduling policy.
arXiv.org
2020
Christos Mavridis, Nilesh Suriyarachchi, John Baras
Considers the problem of defending against adversarial attacks from UAV swarms performing complex maneuvers,driven by multiple, dynamically changing, leaders.
GameSec 2020 Conference
Nariman Torkzaban, John Baras
Introduces a framework for the path-based trust-aware service chain embedding problem. The paper extends a previous work on trust-aware service chain embedding with generalizing the role of trust by incorporating the trustworthiness of the service network links and substrate network paths into the SFC embedding decision process.
arXiv.org
Nariman Torkzaban, Anousheh Gholami, Chrysa Papagianni, John Baras
Introduces the joint satellite gateway placement and routing problem over an ISTN, for facilitating terrestrial-satellite communications while adhering to propagation latency requirements, in a cost-optimal manner. The corresponding load between selected gateways is also balanced.
arXiv.org
Mohammad Mamduhi, Dipankar Maity, John Baras, Karl Johansson
In the design of cyber-physical systems (CPS) where multiple heterogeneous physical systems are coupled via a communication network, a key aspect is to study how network services are distributed among the users. The authors derive the joint optimal time-sensitive control and service allocation policies for each physical system.
KTH Royal Institute of Technology, Stockholm
Erfaun Noorani, Yagiz Savas, Alec Koppel, John Baras, Ufuk Topcu, Brian M. Sadler
In this wireless networks paper, the authors formulate a subset selection problem that aims to find a subset of agents, each of which is equipped with an idealisotropic antenna, that forms a reliable communication linkwith a client through beamforming. They present three algorithms for solving the subset selection problem, and discussed their computational complexity and optimality. All the proposed algorithms can be thought of as attempts towards approximate trade-off analysis and attempts towards finding desirable Pareto points.
arXiv.org
2023
Arda Aydin, Max Alekseyev, Alexander Barg
The authors construct a new family of permutationally invariant codes that correct t Pauli errors for any t ě 1. We also show that codes in the new family correct spontaneous decay errors as well as deletion errors. In many cases the codes in this family are shorter than the best previously known explicit families of permutationally invariant codes for Pauli errors, deletions, and for the amplitude damping channel.
arXiv.org
Adway Patra, Alexander Barg
Node repair on graphs is a recent variation of the distributed storage model, where connections between the storage nodes are described by a graph. Here the authors study this problem under the assumption that some of the nodes act as adversaries, altering the data that they store. They derive bounds on the communication complexity of repair and construct codes that support repair in the presence of adversarial nodes.
2023 IEEE International Symposium on Information Theory (ISIT)
Madhura Pathegama, Alexander Barg
The action of a noise operator on a code transforms it into a distribution on the respective space. Some common examples from information theory include Bernoulli noise acting on a code in the Hamming space and Gaussian noise acting on a lattice in the Euclidean space. We aim to characterize the cases when the output distribution is close to the uniform distribution on the space, as measured by Rényi divergence of order α ∈ [1, ∞]. A version of this question is known as the channel resolvability problem in information theory, and it has implications for security guarantees in wiretap channels, error correction, discrepancy, worst-to-average case complexity reductions, and many other problems. This work quantifies the requirements for asymptotic uniformity (perfect smoothing) and identifies explicit code families that achieve it under the action of the Bernoulli and ball noise operators on the code. The authors derive expressions for the minimum rate of codes required to attain asymptotically perfect smoothing.
arXiv.org
Shubham Jain, Joseph Iosue, Alexander Barg, Victor Albert
The authors develop a framework that yields generalizations of a class of bosonic codes called "cat codes" and unifies such codes with several others. Our key observation is that all such codes are particular instances of quantum versions of spherical codes, a family well known in classical coding theory. We overview the framework and demonstrate its utility with several new multimode cat codes.
arXiv.org
2022
Adway Patra, Alexander Barg
A continuation of a study of regenerating codes in distributed storage systems where connections between the nodes are constrained by a graph. In this problem, the failed node downloads the information stored at a subset of vertices of the graph for the purpose of recovering the lost data.
arXiv.org
Alexander Barg, Moshe Schwartz, Lev Yohananov
A storage code on a graph is a set of assignments of symbols to the vertices such that every vertex can recover its value by looking at its neighbors. The authors consider the question of constructing large-size storage codes on triangle-free graphs. They construct such codes of rate asymptotically approaching one, thereby offering a complete solution to this problem. Equivalently, this question can be phrased as a version of hat-guessing games on graphs. In this language, the authors construct triangle-free graphs with success probability of the players approaching one as the number of vertices tends to infinity. Equivalently again, there exist linear index codes on such graphs of rate approaching zero.
arXiv.org
Alexander Barg, Alexey Glazyrin, Wei-Jiun Kao, Ching-Yi Lai, Pin-Chieh Tseng, Wei-Hsuan Yu
The paper addresses the maximum size of binary codes and binary constant weight codes with few distances. Previous works established a number of bounds for these quantities as well as the exact values for a range of small code lengths. The researchers determine the exact size of maximal binary codes with two distances for all lengths n ≥ 6 as well as the exact size of maximal binary constant weight codes with 2, 3, and 4 distances for several values of the weight and for all but small lengths.
arXiv.org
Adway Patra, Alexander Barg
The authors consider the use of regenerating codes in distributed storage systems where connections between the nodes are constrained by a graph.
2022 IEEE International Symposium on Information Theory (ISIT)
Alexander Barg, Ohad Elishco, Ryan Gabrys, Eitan Yaakobi
A storage code is an assignment of symbols to the vertices of a connected graph G(V, E) with the property that the value of each vertex is a function of the values of its neighbors, or more generally, of a certain neighborhood of the vertex in G. Under the name of recoverable systems, a class of storage codes on Z was recently studied relying on methods from constrained systems and ergodic theory. In this work, the authors address the question of the maximum capacity of recoverable systems on Z and Z2 from a combinatorial perspective. They establish a closed form formula for the capacity of several one- and two-dimensional systems, depending on their recovery set, using connections between storage codes, graphs, anticodes, and difference-avoiding sets.
2022 IEEE International Symposium on Information Theory (ISIT)
Alexander Barg, Ching-Yi Lai, Pin-Chieh Tseng, Wei-Hsuan Yu
A study of the maximum cardinality problem of a set of few distances in the Hamming and Johnson spaces. The authors formulate semidefinite programs for this problem and extend the 2011 works by Barg-Musin and Musin-Nozaki. They find new parameters for which the maximum size of two- and three-distance sets is known exactly.
arXiv.org
2021
Alexander Barg, Gilles Zémor
This paper considers a class of codes on graphs known as storage codes. The authors construct infinite families of linear storage codes with high rate relying on coset graphs of binary linear codes. They also derive necessary conditions for such codes to have high rate, and even rate potentially close to one.
arXiv.org
Ohad Elishco, Alexander Barg
Motivated by the established notion of storage codes, we consider sets of infinite sequences over a finite alphabet such that every k -tuple of consecutive entries is uniquely recoverable from its l -neighborhood in the sequence.
2021 IEEE International Symposium on Information Theory (ISIT)
Adway Patra, Alexander Barg
A study of the problem of erasure correction (node repair) for regenerating codes defined on graphs wherein the cost of transmitting the information to the failed node depends on the graphical distance from this node to the helper vertices of the graph.
arXiv.org
Alexander Barg, Zitan Chen, Itzhak Tamo
The authors construct a family of linear maximally recoverable codes with locality r and dimension r + 1. For codes of length n with r ≈ nα, 0 ≤ α ≤ 1 the code alphabet is of the order n1+3α, which improves upon the previously known constructions of maximally recoverable codes.
arXiv.org
Alexander Barg, Lara Dolecek, Ryan Gabrys, Gyula Katona, Janos Korner, Andrew McGregor, Olgica Milenkovic, Sihem Mesnager, Gilles Zemor
In this guest editorial for a special issue dedicated to Vladimir Iosifovich Levenshtein, Barg and the other guest editors express their admiration of Levenshtein's contributions to combinatorics, coding, and information theory, his elegant problem formulations, ingenious algorithmic solutions, and highly original proof techniques.
IEEE Transactions on Information Theory
Alexander Barg, Peter Boyvalenkov, Maya Stoyanova
The authors derive upper and lower bounds on the sum of distances of a spherical code of size N in n dimensions when N „ nα, 0 ă α ď 2. The bounds are derived by specializing recent general, universal bounds on energy of spherical sets.
arXiv.org
2020
Zitan Chen, Min Ye, Alexander Barg
Addresses two aspects of the repair problem of Reed-Solomon codes.
2020 IEEE International Symposium on Information Theory (ISIT)
Zitan Chen, Alexander Barg
Locally recoverable (LRC) codes form a family of erasure codes, motivated by applications in distributed storage, that support repair of a failed storage node by contacting a small number of other nodes in the cluster. This paper presents two results regarding codes with hierarchical locality and codes with availability.
2020 IEEE International Symposium on Information Theory (ISIT)
Ohad Elishco, Alexander Barg
Motivated by the established notion of storage codes, the authors consider sets of infinite sequences over a finite alphabet such that every k-tuple of consecutive entries is uniquely recoverable from its l-neighborhood in the sequence.
arXiv.org
Alexander Barg, Maxim Skriganov
Shows that the behavior of discrepancies in the Hamming space differs fundamentally because the volume of the ball in this space depends on its radius exponentially while such a dependence for the Riemannian manifolds is polynomial.
arXiv.org
Alexander Barg
Considers the case of finite metric spaces, relating the quadratic discrepancy of a subset to a certain function of the distribution of distances in it. Using linear programming, the author finds several bounds on the minimal discrepancy and give examples of minimizing configurations. In particular, we show that all binary perfect codes have the smallest possible discrepancy.
arXiv.org
Zitan Chen, Alexander Barg
The work focuses on cyclic constructions of LRC codes and derives conditions on the zeros of the code that support the property of hierarchical locality. The authors obtain a general family of hierarchical LRC codes for a new range of code parameters.
arXiv.org
Zitan Chen, Min Ye, Alexander Barg
Reed-Solomon codes possess a repair scheme that supports repair of failed nodes with optimal repair bandwidth. This paper extends this result in two directions.
arXiv.org
2023
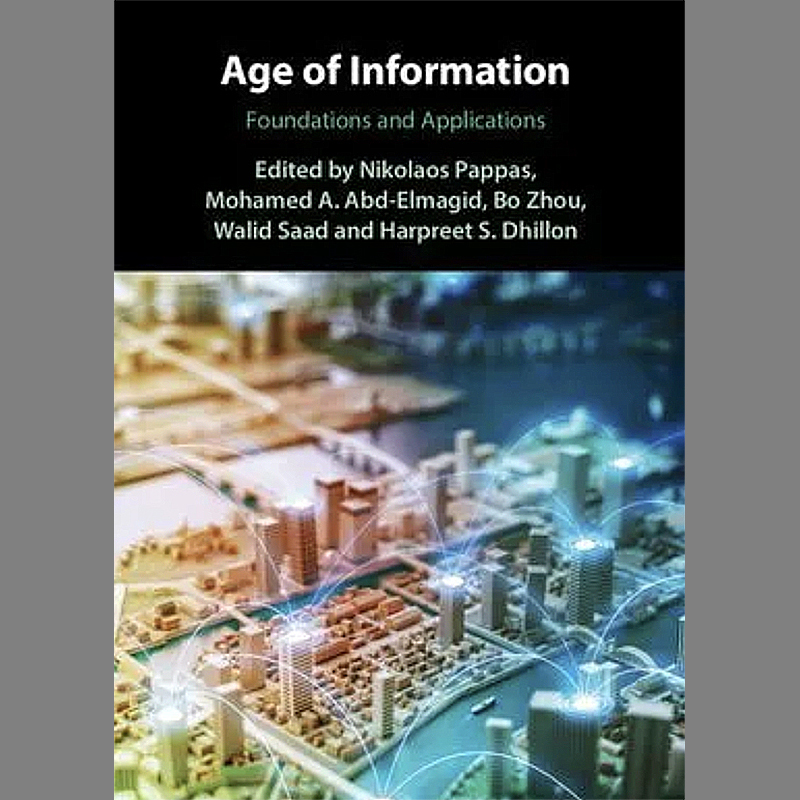
Ali Nikkhah, Anthony Ephremides, Nikolaos Pappas
An investigation into a model relevant to semantics-aware goal-oriented communications, and a proposal for a new metric that incorporates the utilization of information in addition to its timelines. Specifically, the authors consider the transmission of observations from an external process to a battery-powered receiver through status updates.
arXiv.org
Subhankar Banerjee, Sennur Ulukus, Anthony Ephremides
The authors consider a time-slotted communication network consisting of a base station (BS), an adversary, N users and Ns communication channels. They show that a Nash equilibrium may or may not exist for this communication network, and identify special cases where a Nash equilibrium always exists.
Journal of Communications and Networks
Onur Ayan, Sandra Hirche, Anthony Ephremides, Wolfgang Kellerer
Control over networks is envisioned to be one of the driving applications of future mobile networks. Networked control systems contain sensors and controllers exchanging time-sensitive information to fulfill a particular control goal. In this work, the authors consider N heterogeneous feedback control loops closed over a wireless star network. A centralized scheduler located at the central node, i.e., base station (BS), determines the transmission schedule of sensor-to-BS and BS-to-controller communication links. They assume that each link can accommodate a single transmission at a time and is prone to data losses with time-varying probability. Moreover, each controller estimates the system state remotely based on available information. In such a setting, they formulate an optimization problem to minimize the network-induced estimation error at the controller. In particular, they determine the optimal transmission schedule on each link that leads to the minimum normalized mean squared error (nMSE) in a given finite horizon (FH).
IEEE/ACM Transactions on Networking
Yutao Chen, Anthony Ephremides
The authors consider a transmitter-receiver pair in a slotted-time system. The transmitter observes a dynamic source and sends updates to a remote receiver through an error-free communication channel that suffers a random delay. Two cases are considered. In the first case, the update is guaranteed to be delivered within a certain number of time slots. In the second case, the update is immediately discarded once the transmission time exceeds a predetermined value. The receiver estimates the state of the dynamic source using the received updates. The authors adopt the Age of Incorrect Information (AoII) as the performance metric and investigate the problem of optimizing the transmitter’s action in each time slot to minimize AoII.
arXiv.org
Konstantinos Bountrogiannis, Anthony Ephremides, Panagiotis Tsakalides, George Tzagkarakis
The Age of Incorrect Information (AoII) is a recently proposed metric for real-time remote monitoring systems. In particular, AoII measures the time the information at the monitor is incorrect, weighted by the magnitude of this incorrectness, thereby combining the notions of freshness and distortion. This paper addresses the definition of an AoII-optimal transmission policy in a discrete-time communication scheme with a resource constraint and a hybrid automatic repeat request (HARQ) protocol.
arXiv.org
Junjie Wu, Wei Chen, Anthony Ephremides
Extremely low-latency communication has attracted considerable recent attention because it holds the promise of supporting emerging real-time applications such as autonomous driving, smart grids, and Industrial Internet of Things (IIoT). Owing to the limited bandwidth in wireless environments, the sub-packets or even bits have to be transmitted successively, thereby inducing non-negligible delay-induced cost for real-time remote monitoring, estimation, decision making, and control. In this paper, the authors present a unified incremental decoding framework for real-time applications, the costs of which are extremely sensitive to the latency of each individual sub-packet or bit. In contrast to conventional methods, in which a decision is made after fully decoding the entire packet, the incremental decoding strategy allows monitors or actors to make their decisions in real time based on partially received packet.
IEEE Transactions on Communications
Subhankar Banerjee, Sennur Ulukus, Anthony Ephremides
The paper answers the question, "What is the optimal action for the BS when it receives a fresh update packet while an old update packet is being served; should the BS preempt the old packet and transmit the new packet with lower probability of successful transmission q1, or should it discard the new packet and continue to transmit the old packet with higher probability of successful transmission q2."
arXiv.org
Emmanouil Fountoulakis, Themistoklis Charalambous, Anthony Ephremides, Nikolaos Pappas
In 5G and beyond communication systems, the notion of latency gets great momentum in wireless connectivity as a metric for serving real-time communications requirements. However, in many applications, research has pointed out that latency could be inefficient to handle applications with data freshness requirements. Recently, the Age of Information (AoI) metric, which can capture the freshness of the data, has attracted a lot of attention. Here, the authors consider mixed traffic with time-sensitive users; a deadline-constrained user, and an AoI-oriented user. To develop an efficient scheduling policy, they cast a novel optimization problem formulation for minimizing the average AoI while satisfying timely throughput constraints. The formulated problem is cast as a Constrained Markov Decision Process (CMDP). Simulation results show the convergence of the algorithms for different values of the weighted factor and the trade-off between the AoI and timely throughput.
IEEE Transactions on Communications
Ali Nikkhah, Anthony Ephremides, Nikolaos Pappas
The authors consider a wireless power transfer model where the destination receives energy from a dedicated power transmitter and occasionally from the data transmitter. They provide the analysis for the Age of Information (AoI). Furthermore, they propose a new metric, namely the Age of Actuation (AoA) which is relevant when the receiver utilizes the status updates to perform actions in a timely manner.
arXiv.org
Subhankar Banerjee, Sennur Ulukus, Anthony Ephremides
This work considers a time slotted communication system consisting of a base station (BS) and a user. At each time slot an update packet arrives at the BS with probability p, and the BS successfully transmits the update packet with probability q over an erasure channel. The authors assume that the BS has a unit size buffer where it can store an update packet upon paying a storage cost c. There is a trade-off between the age of information and the storage cost. This trade-off is formulated as a Markov decision process and find an optimal switching type storage policy.
arXiv.org
Subhankar Banerjee, Sennur Ulukus, Anthony Ephremides
We consider a time slotted communication network consisting of a base station (BS), an adversary, N users and Ns communication channels. In the first part of the paper, we consider the setting where Ns communication channels Ns are heterogeneously divided among N users. The BS transmits an update to the ith user on a subset of the communication channels Ns,i where Ns,i ∩ Ns,j is not necessarily an empty set. At each time slot, the BS transmits an update packet to a user through a communication channel and the adversary aims to block the update packet sent by the BS by blocking a communication channel. The BS has n discrete transmission power levels to communicate with the users and the adversary has m discrete blocking power levels to block the communication channels. The probability of successful transmission of an update packet depends on these power levels. The BS and the adversary have a transmission and blocking average power constraint, respectively. We provide a universal lower bound for the average age of information for this communication network. We prove that the uniform user choosing policy, the uniform communication channel choosing policy with any arbitrary feasible transmission power choosing policy is 4 optimal; and the max-age user choosing policy, the uniform communication channel choosing policy with any arbitrary feasible transmission power choosing policy is 2 optimal. In the second part of the paper, we consider the setting where the BS chooses a transmission policy and the adversary chooses a blocking policy from the set of randomized stationary policies and Ns,i = Ns for all i, i.e., all users can receive updates on all channels. We show that a Nash equilibrium may or may not exist for this communication network, and identify special cases where a Nash equilibrium always exists.
arXiv.org
Yuotao Chen, Anthony Ephremides
This paper investigates the Age of Incorrect Information (AoII) in a communication system whose channel suffers a random delay. The authors analyze and calculate the performance of the threshold policy in terms of the achieved AoII.
arXiv.org
2022
Clement Kam, Sastry Kompella, Anthony Ephremides
This work studies the role of Age of Information (AoI) in the network state updating process for wireless software defined networks (SDN).
2022 20th International Symposium on Modeling and Optimization in Mobile, Ad hoc, and Wireless Networks (WiOpt)
Ali Maatouk, Mohamad Assaad, Anthony Ephremides
The paper provides an analysis of a status update system modeled through the Stochastic Hybrid Systems (SHSs) tool. The authors provide an approach, dubbed as the moment closure technique, to compute the m-th moment of the age process for any m≥1. Interestingly, this technique allows the approximation of the average age of various systems by solving a simple set of linear equations.
2022 IEEE International Symposium on Information Theory (ISIT)
Yutao Chen, Anthony Ephremides
This paper considers optimizing the performance of a transmitter-receiver system measured by the Age of Incorrect Information (AoII). It aims to optimize the transmitter decision in each time slot to minimize the AoII of the system.
arXiv.org
Yutao Chen, Anthony Ephremides
This paper considers the problem of minimizing the Age of Incorrect Information in a slotted-time system with a transmitter-receiver pair. The authors adopt the Age of Incorrect Information (AoII) as the performance metric and investigate the problem of optimizing the transmitter’s action in each time slot to minimize AoII.
arXiv.org
Yutao Chen, Anthony Ephremides
This paper investigates the problem of minimizing the Age of Incorrect Information (AoII) when the communication channel has a random delay. The authors consider a slotted-time system where a transmitter observes a dynamic source and decides when to send updates to a remote receiver through a channel with random delay. The receiver maintains estimates of the state of the dynamic source based on the received updates. AoII is adopted as the performance metric and the authors investigate the problem of optimizing the transmitter’s action in each time slot to minimize AoII.
arXiv.org
Shaoling Hu, Junjie Wu, Wei Chen, Anthony Ephremides
Real-time monitoring and remote control of stochastic systems have attracted considerable attention due to their potential in task-oriented communications and industrial Internet of Things (IIoT). How to achieve ultra high-freshness in real-time monitoring and remote control becomes a challenging problem. This paper examines freshness-oriented source coding with incremental decoding in contrast to conventional source encoding/decoding.
2021 IEEE Global Communications Conference (GLOBECOM)
2021
Clement Kam, Sastry Kompella, Anthony Ephremides
A study of the problem of a two-user, single-channel cognitive radio network, in which the objective is to maximize the secondary user throughput subject to a constraint on the probability of collision experienced by the primary user. The authors apply a Lyapunov framework to identify the tradeoff between three fundamental information qualities: AoI, accuracy, and completeness. Characterizing these types of tradeoffs can be a useful intermediate step towards optimizing a variety of objectives.
IEEE Military Communications Conference (MILCOM) 2021
Yuotao Chen, Anthony Ephremides
The authors study a slotted-time system where a base station needs to update multiple users at the same time. Due to the limited resources, only part of the users can be updated in each time slot. They consider the problem of minimizing the Age of Incorrect Information (AoII) when imperfect Channel State Information (CSI) is available.
Entropy Special Issue on Age of Information: Concept, Metric and Tool for Network Control
Clement Kam, Sastry Kompella, Anthony Ephremides
Age of information is often studied as a primary objective to be optimized, but for problems where age is not the primary objective, it can still have a major role that can be utilized. This work studies a two-user, single-channel cognitive radio network, where the primary user’s transmit/idle dynamics are modeled as a binary Markov chain, and the secondary user decides to either sense or transmit. The authors transform the problem by converting the randomized policy to its induced age distribution function. As a result, the age distribution-based formulation results in a linear program, which can be solved efficiently.
19th International Symposium on Modeling and Optimization in Mobile, Ad hoc, and Wireless Networks (WiOpt 2021)
Sheng Zhou, Zhiyuan Jiang, Nikolaos Pappas, Anthony Ephremides, Luis DaSilva
This special issue is focused on the AoI-inspired sensing, communication, and control co-design in IoT systems.
IEEE Internet of Things Journal
Emmanouil Fountoulakis, Themistoklis Charalambous, Anthony Ephremides, Nikolaos Pappas
In 5G and beyond systems, the notion of latency is being considered in wireless connectivity as a metric for serving real-time communications requirements. However, research indicates that latency could be inefficient to handle applications with data freshness requirements. Recently, the notion of Age of Information (AoI) that can capture the freshness of the data has attracted attention. The authors consider mixed traffic with time-sensitive users; a deadline-constrained user, and an AoI-oriented user. To develop an efficient scheduling policy, they cast a novel optimization problem formulation for minimizing average AoI while satisfying timely throughput constraints.
arXiv.org
Ali Maatouk, Mohamad Assaad, Anthony Ephremides
The authors analyze status update systems modeled through the Stochastic Hybrid Systems (SHSs) tool.
arXiv.org
Emmanouil Fountoulakis; Nikolaos Pappas; Anthony Ephremides
Future wireless networks will be characterized by users with heterogeneous requirements. Such users can require low-latency or minimum-throughput requirements. In addition, due to the limited-power budget of the mobile devices, a power-efficient scheduling scheme is required by the network. In this work, the authors cast a stochastic network optimization problem for minimizing the packet drop rate while guaranteeing a minimum throughput and taking into account the limited-power capabilities of the users.
IEEE Conference on Computer Communications Workshops (Infocom 2021)
Elif Uysal, Onur Kaya, Anthony Ephremides, James Gross, Marian Codreanu, Petar Popovski, Mohamad Assaad, Gianluigi Liva, Andrea Munari, Touraj Soleymani, Beatriz Soret, Karl Henrik Johansson
A vision for a departure from the established way of architecting and assessing communication networks, by incorporating the semantics of information for communications and control in networked systems.
arXiv.org
Onur Ayan, Anthony Ephremides, Wolfgang Kellerer
The authors consider N heterogeneous control sub-systems sharing a wireless communication channel. Network resources are limited and are allocated by a centralized scheduler. Each transmission is lost with a probability that is higher or lower depending on the portion each sub-system receives from the pool of network resources. Furthermore, state measurements go through a first come first serve (FCFS) Geo/Geo/1 transmission queue after they are generated by each sensor. In such a setting, the information at each remote controller that is observing the state measurements through the wireless channel gets outdated. Age of Information (AoI)captures this effect and measures the information freshness a teach controller. By definition, AoI is control unaware thus not a standalone metric to capture the heterogeneous requirements of control sub-systems. However, we show how the stationary distribution of Age of information (AoI) can be employed as an intermediate metric to obtain the expected control performance in the network. As a result, we solve the resource allocation problem optimally and show by simulations that we are able to improve the control performance indirectly through AoI.
IEEE INFOCOM: Age of Information Workshop 2021
Emmanouil Fountoulakis, Marian Codreanu, Anthony Ephremides, Nikolaos Pappas
This work considers the problem of jointly minimizing the average cost of sampling and transmitting status updates by users over a wireless channel subject to average Age of Information (AoI) constraints.
arXiv.org
Yuotao Chen, Anthony Ephremides
Age of Incorrect Information (AoII) is a newly introduced performance metric that is adaptable to a variety of communication goals. The fundamental nature of AoII has been elusive so far. In this work, the authors consider the AoII in a system where a transmitter sends updates about a multi-state Markovian source to a remote receiver through an unreliable channel. The communication goal is to minimize AoII subject to a power constraint. The problem is cast into a Constrained Markov Decision Process. The research proves that the optimal policy is a mixture of two deterministic threshold policies.
arXiv.org
2020
Ali Maatouk, Yin Sun, Anthony Ephremides, and Mohamad Assaad
The authors consider a scheduling problem in which several streams of status update packets with different priority levels are sent through a shared channel to their destinations. They introduce a notion of lexicographic age optimality, or simply lex-age-optimality, to evaluate the performance of multi-class status update policies.
18th International Symposium on Modeling and Optimization in Mobile, Ad Hoc, and Wireless Networks (WiOpt 2020)
Emmanouil Fountoulakis, Nikolaos Pappas, Anthony Ephremides
Future wireless networks will be characterized by heterogeneous traffic requirements. Such requirements can below-latency or minimum-throughput, so the network must adjust to different needs. Usually, users with low-latency requirements have to deliver their demand within a specific time frame, i.e., before a deadline, and they co-exist with throughput-oriented users. In addition, the users are mobile and they share the same wireless channel. Therefore, they have to adjust their power transmission to achieve reliable communication. However, due to the limited-power budget of wireless mobile devices, a power-efficient scheduling scheme is required by the network. The authors cast a stochastic network optimization problem for minimizing the packet drop rate while guaranteeing a minimum-throughput and taking into account the limited-power capabilities of the users.
arXiv.org
Ali Maatouk, Saad Kriouile, Mohamad Assaad, Anthony Ephremides
This paper considers the average age minimization problem where a central entity schedules M users among the N available users for transmission over unreliable channels.
2020 IEEE International Symposium on Information Theory (ISIT)
Clement Kam, Sastry Kompella, Anthony Ephremides
For monitoring applications, the Age of Information (AoI) metric has been the primary focus of recent research, but closely related to monitoring is the problem of real-time or remote estimation. Age of Information has been shown to be insufficient for minimizing remote estimation error, but recently a metric known as Age of Incorrect Information (AoII) was proposed that characterizes the cost of a monitor being in an erroneous state over time. This work studies the AoII metric in the simple context of monitoring a symmetric binary information source over a delay system with feedback. It compares three different performance metrics: real-time error, AoI, and AoII. For each metric, the optimal sampling problem as a Markov decision process is formulated. A dynamic programming algorithm to compute the optimal performance and policy is applied.
2020 IEEE Conference on Computer Communications Workshops (INFOCOM WKSHPS)
Meng Wang, Wei Chen, Anthony Ephremides
One of the most critical problems for the emerging Internet of Things is the real-time remote reconstruction of ongoing signals (or their functions) from a set of measurements that are under-sampled and delayed in the network. The authors address this problem under three special sampling policies.
IEEE Transactions on Information Theory
Emmanouil Fountoulakis, Nikolaos Pappas, Marian Codreanu, Anthony Ephremides
Considers the problem of minimizing the time average cost of sampling and transmitting status updates by users over a wireless channel subject to average Age of Information constraints. A stochastic optimization problem is formulated and solved with a dynamic algorithm that takes decisions in a slot-by-slot basis.
arXiv.org
Antzela Kosta, Nikolaos Pappas, Anthony Ephremides, Vangelis Angelakis
Investigates a sample path of the age of information (AoI) stochastic process and provides a general framework that establishes a relation among the AoI, the system delay, and the peak AoI. The aim is to be able to analyze any non-linear function of AoI and provide a wide range of potential uses of information ageing depending on the application.
arXiv.org
Ali Maatouk, Yin Sun, Anthony Ephremides, Mohamad Assaad
Introduces the idea of lex-age-optimality that captures both age-optimality and the order of time-cruciality betweeen streams in a general multi-class priority-based scheduling scenario.
Laboratoire des Signaux & Systemes, L2S Central Supelec, France
Ali Maatouk, Saad Kriouile, Mohamad Assaad, Tony Ephremides
The authors prove that the Whittle’s index policy is age-optimal for the general asymmetrical case in the burgeoning many-users regime of Internet of Things interconnected devices.
arXiv.org
2019
Song Huang, Di Yuan, Anthony Ephremides
This article related to spectrum scarcity studies bandwidth partition and allocation to optimize spectrum utilitzation in cognitive communications under the interweave paradigm.
IEEE Journal of Communications & Networks
2023
Ahmed Adel Attia, Yashish Siriwardena, Carol Espy-Wilson
The performance of deep learning models depends significantly on their capacity to encode input features efficiently and decode them into meaningful outputs. Better input and output representation has the potential to boost models' performance and generalization. In the context of acoustic-to-articulatory speech inversion (SI) systems, the authors study the impact of utilizing speech representations acquired via self-supervised learning (SSL) models, such as HuBERT compared to conventional acoustic features. Additionally, they investigate the incorporation of novel tract variables (TVs) through an improved geometric transformati
Harvard ads Labs, arXiv.org
Ahmed Adel Attia, Jing Liu, Wei Ai, Dorottya Demszky, Carol Espy-Wilson
Recent advancements in Automatic Speech Recognition (ASR) systems, exemplified by Whisper, have demonstrated the potential of these systems to approach human-level performance given sufficient data. However, this progress doesn't readily extend to ASR for children due to the limited availability of suitable child-specific databases and the distinct characteristics of children's speech. A recent study investigated leveraging the My Science Tutor (MyST) children's speech corpus to enhance Whisper's performance in recognizing children's speech. The authors were able to demonstrate some improvement on a limited testset. This paper builds on these findings by enhancing the utility of the MyST dataset through more efficient data preprocessing.
Harvard ads Labs, arXiv.org
Liran Oren, Brittany Fletcher, Huy Le, Yashish Maduwantha, Carol Espy-Wilson, Mark Tiede, Suzanne Boyce
This study focuses on the correlation between indirect and direct methods of assessing both timing and magnitude of velopharyngeal opening for coarticulation using complementary data from nasometry and a novel technique – high-speed nasopharyngoscopy.
The Journal of the Acoustical Society of America
Yashish Siriwardena, Ahmed Adel Attia, Ganesh Sivaraman, Carol Espy-Wilson
Data augmentation has proven to be a promising prospect in improving the performance of deep learning models by adding variability to training data. In previous work with developing a noise robust acoustic-to-articulatory speech inversion (SI) system, the authors have shown the importance of noise augmentation to improve the performance of speech inversion in ‘noisy’ speech conditions. In this work, they extend the idea of data augmentation to improve the SI systems on both clean speech and noisy speech data by experimenting three data augmentation methods. They also propose a Bidirectional Gated Recurrent Neural Network as the speech inversion system instead of the previously used feed forward neural network.
2023 31st European Signal Processing Conference (EUSIPCO)
Ahmed Adel Attia, Jing Liu, Wei Ai, Dorottya Demszky, Carol Espy-Wilson
Recent advancements in Automatic Speech Recognition (ASR) systems, exemplified by Whisper, have demonstrated the potential of these systems to approach human-level performance given sufficient data. However, this progress doesn’t readily extend to ASR for children due to the limited availability of suitable child-specific databases and the distinct characteristics of children’s speech. This paper enhances the utility of the MyST dataset through more efficient data preprocessing.
arXiv.org
Ahmed Adel Attia, Yashish M. Siriwardena, Carol Espy-Wilson
The performance of deep learning models depends significantly on their capacity to encode input features efficiently and decode them into meaningful outputs. Better input andoutput representation has the potential to boost models’ performance and generalization. In the context of acoustic-to-articulatory speech inversion (SI) systems, the authors study the ,impact of utilizing speech representations acquired via self-supervised learning (SSL) models, such as HuBERT compared to conventional acoustic features. Additionally, they investigate the incorporation of novel tract variables (TVs) through an improved geometric transformation model.
arXiv.org
Yashish Siriwardena, Carol Espy-Wilson, Suzanne Boyce, Mark Tiede, Liran Oren
The researchers evaluate the degree to which the nasalance measure reflects fine-grained patterns of VP movement by comparison with simultaneously collected direct measures of VP opening using high-speed nasopharyngoscopy (HSN). They show that nasalance is significantly correlated with the HSN signal, and that both match expected patterns of nasality. They also train a temporal convolution-based speech inversion system in a speaker-independent fashion to estimate VP movement for nasality, using nasalance as the ground truth.
arXiv.org
Nina Benway, Yashish Siriwardena, Jonathan L Preston, Elaine Hitchcock, Tara McAllister, Carol Espy-Wilson
Acoustic-to-articulatory speech inversion could enhance automated clinical mispronunciation detection to provide detailed articulatory feedback unattainable by formant-based mispronunciation detection algorithms; however, it is unclear the extent to which a speech inversion system trained on adult speech performs in the context of (1) child and (2) clinical speech. In the absence of an articulatory dataset in children with rhotic speech sound disorders, we show that classifiers trained on tract variables from acoustic-to-articulatory speech inversion meet or exceed the performance of state-of-the-art features when predicting clinician judgment of rhoticity.
arXiv.org
Ahmed Attia, Mark Tiede, Carol Espy-Wilson
Accurate analysis of speech articulation is crucial for speech analysis. However, X-Y coordinates of articulators strongly depend on the anatomy of the speakers and the variability of pellet placements, and existing methods for mapping anatomical landmarks in the X-ray Microbeam Dataset (XRMB) fail to capture the entire anatomy of the vocal tract. In this paper, the researchers propose a new geometric transformation that improves the accuracy of these measurements. Their transformation maps anatomical landmarks' X-Y coordinates along the midsagittal plane onto six relative measures: Lip Aperture (LA), Lip Protusion (LP), Tongue Body Constriction Location (TTCL), Degree (TBCD), Tongue Tip Constriction Location (TTCL) and Degree (TTCD). This contribution is the extension of the palate trace towards the inferred anterior pharyngeal line, which improves measurements of tongue-body constriction.
arXiv.org
2022
Yashish Siriwardena, Carol Espy-Wilson, Shihab Shamma
Most organisms including humans function by coordinating and integrating sensory signals with motor actions to survive and accomplish desired tasks. Learning these complex sensorimotor mappings proceeds simultaneously and often in an unsupervised or semi-supervised fashion. An autoencoder architecture (MirrorNet) inspired by this sensorimotor learning paradigm is explored in this work to learn how to control an articulatory synthesizer.
arXiv.org
Yashish Siriwardena, Carol Espy-Wilson
This work incorporates acoustically derived source features, aperiodicity, periodicity and pitch as additional targets to an acoustic-to-articulatory speech inversion (SI) system. The authors also propose a Temporal Convolution based SI system, which uses auditory spectrograms as the input speech representation, to learn long-range dependencies and complex interactions between the source and vocal tract, to improve the SI task.
arXiv.org
Ahmed Adel Attia, Carol Espy-Wilson
A deep learning-based approach using Masked Autoencoders to accurately reconstruct the mistracked articulatory recordings for 41 out of 47 speakers of the XRMB dataset. (The University of Wisconsin X-Ray Microbeam (XRMB) dataset is one of various datasets that provide articulatory recordings synced with audio recordings.) The authors' model is able to reconstruct articulatory trajectories that closely match ground truth, even when three out of eight articulators are mistracked, and retrieve 3.28 out of 3.4 hours of previously unusable recordings.
arXiv.org
Rahil Parikh, Gaspar Rochette, Carol Espy-Wilson, Shihab Shamma
The authors perform a thorough investigation on ConvTasnet and DPT-Net to analyze how they perform a harmonic analysis of the input mixture.
arXiv.org
Rahil Parikh, Ilya Kavalerov, Carol Espy-Wilson, Shihab Shamma
Recent advancements in deep learning have led to drastic improvements in speech segregation models. Despite their success and growing applicability, few efforts have been made to analyze the underlying principles that these networks learn to perform segregation. The authors analyze the role of harmonicity on two state-of-the-art Deep Neural Networks (DNN)-based models- Conv-TasNet and DPT-Net.
arXiv.org
2021
Yashish Siriwardena, Nadee Seneviratne, Carol Espy-Wilson
Mental health illnesses like Major Depressive Disorder and Schizophrenia affect the coordination between articulatory gestures in speech production. Coordination features derived from Vocal tract variables (TVs) predicted by a speech inversion system can quantify the changes in articulatory gestures and have proven to be effective in the classification of mental health disorders. In this study we use data from the IEMOCAP (acted emotions) and MSP Podcast (natural emotions) datasets to understand how coordination features extracted from TVs can be used to capture changes between different emotions for the first time. We compared the eigenspectra extracted from channel delay correlation matrices for Angry, Sad and Happy emotions with respect to the “Neutral” emotion. Across both the datasets, it was observed that the “Sad” emotion follows a pattern suggesting simpler articulatory coordination while the “Angry” emotion follows the opposite showing signs of complex articulatory coordination. For the majority of subjects, the ‘Happy’ emotion follows a complex articulatory coordination pattern, but has significant confusion with “Neutral” emotion. We trained a Convolutional Neural Network with the coordination features as inputs to perform emotion classification. A detailed interpretation of the differences in eigenspectra and the results of the classification experiments will be discussed.
This is a meeting abstract published in the Journal of the Acoustical Society of America
Carol Espy-Wilson
Dr. Espy-Wilson discusses a speech inversion system her group has developed that maps the acoustic signal to vocal tract variables (TVs). The trajectories of the TVs show the timing and spatial movement of speech gestures. She explains how her group uses machine learning techniques to compute articulatory coordination features (ACFs) from the TVs. The ACFs serve as an input into a deep learning model for mental health classification. Espy-Wilson also illustrates the key acoustic differences between speech produced by subjects when they are mentally ill relative to when they are in remission and relative to healthy controls. The ultimate goal of this research is the development of a technology (perhaps an app) for patients that can help them, their therapists and caregivers monitor their mental health status between therapy sessions.
Keynote speech at the 2021 Acoustical Society of America Annual Meeting, June 8, 2021
View a press release from the Acoustical Society of America about this speech
Nadee Seneviratne, Carol Espy-Wilson
The paper proposes a new multi-stage architecture trained on vocal tract variable (TV)-based articulatory coordination features (ACFs) for depression severity classification which clearly outperforms the baseline models. The authors establish that the robustness of ACFs based on TVs holds beyond mere detection of depression and even in severity level classification. This work can be extended to develop a multi-modal system that can take advantage of textual information obtained through Automatic Speech Recognition tools. Linguistic features can reveal important information regarding the verbal content of a depressed patient relating to their mental health condition.
arXiv.org; accepted for Interspeech2021, Aug. 30-Sept. 3, 2021
Yashish Maduwantha, Chris Kitchen, Deanna L. Kelly, Carol Espy-Wilson
This study, conducted with AIM-HI funding, investigates speech articulatory coordination in schizophrenia subjects exhibiting strong positive symptoms (e.g.hallucinations and delusions), using a time delay embedded correlation analysis. It finds a distinction between healthy and schizophrenia subjects in neuromotor coordination in speech.
ResearchGate.net
2020
Nadee Seneviratne, Carol Espy-Wilson
The paper develops a generalized classifier for depression detection using a dilated convolutional neural network which is trained on articulatory coordination features (ACFs) extracted from two depression databases.
arXiv.org; accepted for Interspeech2021, Aug. 30-Sept. 3, 2021
Nadee Seneviratne, James Williamson, Adam Lammert, Thomas Quatieri, Carol Espy-Wilson
Changes in speech production that occur as a result of psychomotor slowing, a key feature of Major Depressive Disorder(MDD), are used to non-invasively diagnose MDD. In previous work using data from seven subjects, the authors showed that using speech-inverted vocal tract variables (TVs) as a direct measure of articulation to quantify changes in the way speech is produced when depressed relative to being not depressed out-performs formant information as a proxy for articulatory information. In this paper, the authors make significant extensions by using more subjects, taking into account more eigenvalue features and incorporating TVs related to place of articulation and the glottal source, resulting in a significant improvement in accuracy.
Interspeech 2020
2019
Nadee Seneviratne, Ganesh Sivaraman, Carol Espy-Wilson
This paper proposes a multi-corpus speech inversion system for automatic speech recognition, pronounciation training and speech therapy.
Interspeech 2019
Carol Espy-Wilson, Adam Lammert, Nadee Seneviratne, Thomas Quatieri
A new articulary inversion process provides a potentially powerful way of detecting depression based on speech patterns.
Interspeech 2019
Saurabh Sahu, Vikramjit Mitra, Nadee Seneviratne, Carol Espy-Wilson
The paper leverages multi-modal learning and automated speech recognition (ASR) systems toward building a speech-only emotion recognition model.
Interspeech 2019
2021
Michael Lin, Nuno Martins, Richard La
The researchers investigate the problem of designing a task scheduler policy when the efficiency of the server is allowed to depend on the past utilization, which is modeled using an internal state of the server. They propose a new framework for studying the stability of the queue length of the system. They then characterize the set of task arrival rates for which there exists a stabilizing stationary scheduler policy and identify an optimal threshold policy that stabilizes the system whenever the task arrival rate lies in the interior of the aforementioned set for which there is a stabilizing policy.
IEEE Transactions on Control of Network Systems
2020
Michael Lin, Richard La
Develops a new algorithm to position depots where bridge inspection robots would be stored and recharged, and determines a set of sites for each robot to inspect on the bridge.
arXiv.org
Michael Lin, Nuno Martins, Richard La
This work expands on stabilizability results recently obtained for a framework to establish methods to design scheduling policies that not only stabilize the queue but also reduce the utilization rate—understood as the infinite-horizon time-averaged expected portion of time the server is working.
arXiv.org
2022
Rohith Aralikatti, Zhenyu Tang, Dinesh Manocha
The new approach described here improves the performance of learning-based speech dereverberation using accurate synthetic datasets. It is designed to recover the reverb-free signal from a reverberant speech signal.
arXiv.org
2019
Zhenyu Tang, Hsien-Yu Meng, Dinesh Manocha
This paper proposes a method for generating low-frequency compensated synthetic impulse responses that improve the performance of automatic speech recognition, lowering word error rates. This method generates more realistic synthetic IRs with low-frequency compensation for far-field ASR training.
arXiv.org
2023
Semih Kara, Nuno Martins
Kara and Martins report on new sufficient conditions for the stability of evolutionary dynamics in population games. A large number of agents interact noncooperatively in a population game by selecting strategies based on their payoffs. Each agent is allowed to revise its strategy repeatedly with an average frequency referred to as the revision rate. The authors are interested in the case where an agent's current strategy influences directly the revision rate. Existing stability results for this case assume that a memoryless potential game generates the strategies' payoffs. This article extends these results to allow for payoff mechanisms that can be either dynamic or memoryless games that do not have to be potential. The researchers assume that the agents' revision preferences follow a so-called pairwise comparison protocol. These protocols are ubiquitous because they operate fully decentralized and with minimal information requirements (they need to access only the payoff values, not the mechanism). They use a well-motivated example to illustrate an application of their framework.
IEEE Transactions on Control of Network Systems
2021
Michael Lin, Nuno Martins, Richard La
The researchers investigate the problem of designing a task scheduler policy when the efficiency of the server is allowed to depend on the past utilization, which is modeled using an internal state of the server. They propose a new framework for studying the stability of the queue length of the system. They then characterize the set of task arrival rates for which there exists a stabilizing stationary scheduler policy and identify an optimal threshold policy that stabilizes the system whenever the task arrival rate lies in the interior of the aforementioned set for which there is a stabilizing policy.
IEEE Transactions on Control of Network Systems
2020
Michael Lin, Nuno Martins, Richard La
This work expands on stabilizability results recently obtained for a framework to establish methods to design scheduling policies that not only stabilize the queue but also reduce the utilization rate—understood as the infinite-horizon time-averaged expected portion of time the server is working.
arXiv.org
2023
Sagnik Bhattacharya; Prakash Narayan
Shared information is a measure of mutual dependence among m≥2 jointly distributed discrete random variables. A new undirected probabilistic graphical model, a cliqueylon graph, is introduced, with potential applications in leader-follower swarms and neuron clusters with correlations of varying strength. Shared information is characterized explicitly for the cliqueylon, relying on structural properties of an underlying optimization. Implications for the data compression problem of omniscience are highlighted.
2023 IEEE International Symposium on Information Theory (ISIT)
Ajaykrishnan Nageswaran; Prakash Narayan
For a given function of user data, a querier must recover with at least a prescribed probability, the value of the function based on a user-provided query response. Subject to this requirement, the user forms the query response so as to minimize the likelihood of the querier guessing a list of prescribed size to which the data value belongs based on the query response. We obtain a general converse upper bound for the maximum list privacy which is shown to be tight for the special case of a binary-valued function through an explicit achievability scheme for the query response.
arXiv.org
2022
Sagnik Bhattacharya; Prakash Narayan
Shared information is a measure of mutual dependence among m ≥ 2 jointly distributed discrete random variables. For a Markov chain on a tree with a given joint distribution, the authors give a new proof of an explicit characterization of shared information. When the joint distribution is not known, they exploit the special form of this characterization to provide a multiarmed bandit algorithm for estimating shared information, and analyze its error performance.
2022 IEEE International Symposium on Information Theory (ISIT)
2021
Sagnik Bhattacharya; Prakash Narayan
Consider a finite set of multiple sources, described by a random variable with m components. Only k≤m source components are sampled and jointly compressed in order to reconstruct all the m components under an excess distortion criterion. Sampling can be that of a fixed subset A with |A|=k or randomized over all subsets of size k . In the case of random sampling, the sampler may or may not be aware of the m source components. The compression code consists of an encoder whose input is the realization of the sampler and the sampled source components; the decoder input is solely the encoder output. The combined sampling mechanism and rate distortion code are universal in that they must be devised without exact knowledge of the prevailing source probability distribution. In a Bayesian setting, considering coordinated single-shot sampling and compression, our contributions involve achievability results for the cases of fixed-set, source-independent and source-dependent random sampling.
2021 IEEE International Symposium on Information Theory (ISIT)
Ajaykrishnan Nageswaran; Prakash Narayan
A user generates n independent and identically distributed data rvs with a pmf that must be guarded from a querier. The querier must recover, with a prescribed accuracy, a given function of the data from each of n independent and identically distributed user-devised query responses. The user chooses the data pmf and the random query responses to maximize distribution privacy as gauged by the divergence between the pmf and the querier's best estimate of it based on the n query responses. Considering an arbitrary function, a basic achievable lower bound, that does not depend on n, is provided for distribution privacy. Next, upper (converse) and lower (achievable) bounds, dependent on n, are developed that converge to said basic bound as n grows. Explicit strategies for the user and the querier are identified.
2021 IEEE International Symposium on Information Theory (ISIT)
2020
Ajaykrishnan Nageswaran; Prakash Narayan
In this paper, a user generates n independent and identically distributed data random variables with a probability mass function that must be guarded from a querier. The querier must recover, with a prescribed accuracy, a given function of the data from each of n independent and identically distributed user-devised query responses. The user chooses the data pmf and the random query responses to maximize distribution privacy as gauged by the divergence between the pmf and the querier's best estimate of it based on the n query responses. A general lower bound is provided for distribution privacy; and, for the case of binary valued functions, upper and lower bounds that converge to said bound as n grows. Explicit strategies for the user and querier are identified.
2020 IEEE International Symposium on Information Theory (ISIT)
2022
Vincent Hsiao, Dana Nau, Rina Dechter
Bayesian Networks are useful for analyzing the properties of systems with large populations of interacting agents (e.g., in social modeling applications and distributed service applications). These networks typically have large functions (CPTs), making exact inference intractable. However, often these models have additive symmetry. In this paper the authors show how summation-based CPTs, especially in the presence of symmetry, can be computed efficiently through the usage of the Fast Fourier Transform (FFT).
Proceedings of the 25th International Conference on Artificial Intelligence and Statistics (AISTATS) 2022
2021
Sunandita Patra, Alexander Velazquez, Myong Kang, Dana Nau
The authors describe ACR-SDN, a system to monitor, diagnose, and quickly respond to attacks or failures that may occur in software-defined networks (SDNs). An integral part of ACR-SDN is its use of RAE+UPOM, an automated acting and planning engine that uses hierarchical refinement. To advise ACR-SDN on how to recover a target system from faults and attacks, RAE+UPOM uses attack recovery procedures writ-ten as hierarchical operational models. Our experimental results show that the use of refinement planning in ACR-SDN is successful in recovering SDNs from attacks with respect to three performance metrics: estimated time for recovery, efficiency, and retry ratio.
Association for the Advancement of Artificial Intelligence
2022
Yashish Siriwardena, Carol Espy-Wilson, Shihab Shamma
Most organisms including humans function by coordinating and integrating sensory signals with motor actions to survive and accomplish desired tasks. Learning these complex sensorimotor mappings proceeds simultaneously and often in an unsupervised or semi-supervised fashion. An autoencoder architecture (MirrorNet) inspired by this sensorimotor learning paradigm is explored in this work to learn how to control an articulatory synthesizer.
arXiv.org
2023
Yalin E. Sagduyu, Tugba Erpek, Aylin Yener, Sennur Ulukus
The authors introduce a deep learning approach to dynamic spectrum access, leveraging the synergy of multimodal image and spectrum data for the identification of potential transmitters. They consider an edge device equipped with a camera that is taking images of potential objects such as vehicles that may harbor transmitters.
arXiv.org
Orkun Gamgam, Nail Akar, Sennur Ulukus
A study of a scheduling problem in a status update system composed of an arbitrary number of information sources with different service time distributions and weights for the purpose of minimizing the weighted sum age of information.
ADS/ABS Labs, Harvard
Subhankar Banerjee, Sennur Ulukus, Anthony Ephremides
The authors consider a time slotted communication network consisting of a base station (BS), an adversary, N users and Ns communication channels. They show that a Nash equilibrium may or may not exist for this communication network, and identify special cases where a Nash equilibrium always exists.
Journal of Communications and Networks
Shreeya Meel, Sennur Ulukus
Proposes a two-agent function optimization algorithm under information theoretic privacy of feasible sets. The authors' algorithm runs the primitives CarPSI and FindPSI, built on optimal SPIR schemes to find the optimum solution set. In doing so, the information on the feasible set of an agent leaked to the other agent is kept at a minimum. It is shown that both the download cost and the information leakage of our scheme are lower than those of an alternative (naive) scheme that relies on learning the joint feasible set using PSI.
arXiv.org
Priyanka Kaswan, Sennur Ulukus
The authors build a system model with two sources, a reliable source and an unreliable source, who are responsible for disseminating updates regarding a process to an age-based gossip network of n nodes. Nodes wish to have fresh information, however, they have preference for packets that originated at the reliable source and are willing to sacrifice their version age of information by up to G versions to switch from an unreliable packet to a reliable packet. The authors study how this protocol affects the prevalence of unreliable packets at nodes in the network and their version age.
arXiv.org
Yalin E. Sagduyu, Tugba Erpek, Aylin Yener, Sennur Ulukus
This paper explores the integration of deep learning techniques for joint sensing and communications, with an extension to semantic communications.
arXiv.org
Nail Akar, Sennur Ulukus
A study of a remote monitoring system in which a collection of ergodic, aperiodic, mutually independent, and heterogeneous continuous time Markov chain-based information sources are considered.
arXiv.org
Sajani Vithana, Zhusheng Wang, Sennur Ulukus
The authors provide an introduction to basic private information retrieval (PIR) with examples, followed by a brief description of its immediate variants. They then provide a detailed discussion on the conceptual extensions of PIR, along with potential research directions.
IEEE BITS the Information Theory Magazine
Matin Mortaheb, Mohammad (Amir) Khojastepour, Srimat Chakradhar, Sennur Ulukus
A real-time deep learning based H.264 controller is proposed. This controller leverages instantaneous channel quality data driven from the physical layer, along with the video chunk, to dynamically estimate the optimal encoder parameters with a negligible delay in real-time.
arXiv.org
Purbesh Mitra, Sennur Ulukus
The authors consider a gossip network, consisting of n nodes, which tracks the information at a source. The source updates its information with a Poisson arrival process and also sends updates to the nodes in the network. Due to the continuous search space for optimum rate allocation, they formulate this problem as a continuum-armed bandit problem and employ Gaussian process based Bayesian optimization to meet a trade-off between exploration and exploitation sequentially. .
arXiv.org
Cemil Vahapoglu, Timothy J. O’Shea, Tamoghna Roy, Sennur Ulukus
NNBF is an unsupervised deep learning framework for the design of uplink receive multi-user single input multiple output (MU-SIMO) beamforming. The primary objective is to enhance the throughput by focusing on maximizing the sum-rate while also offering computationally efficient solution, in contrast to established conventional methods.
arXiv.org
Matin Mortaheb, Mohammad A. (Amir) Khojastepour, Srimat T. Chakradhar, Sennur Ulukus
Proposes a novel deep learning multi-resolution JSCC framework inspired by the concept of multi-task learning (MTL). This proposed framework excels at encoding data for different resolutions through hierarchical layers and effectively decodes it by leveraging both current and past layers of encoded data. Moreover, this framework holds great potential for semantic communication, where the objective extends beyond data reconstruction to preserving specific semantic attributes throughout the communication process.
arXiv.org
Arunabh Srivastava, Sennur Ulukus
Considers a gossip network consisting of a source forwarding updates and n nodes placed geometrically in a ring formation.
arXiv.org
Sahan Liyanaarachchi, Sennur Ulukus
A study of the structure of the optimal sampling policy to minimize the average age of information when the channel state (i.e., busy or idle) is not immediately perceived by the transmitter upon the delivery of a sample due to random delays in the feedback (ACK) channel. In this setting, the researchers show that it is not always optimal to wait for ACKs before sampling, and thus, early sampling before the arrival of an ACK may be optimal. The authors show that, under certain conditions on the distribution of the ACK delays, the optimal policy is a mixture of two threshold policies.
arXiv.org
Alptug Aytekin, Mohamed Nomeir, Sajani Vithana, Sennur Ulukus
Considers both the classical and quantum variations of X-secure, E-eavesdropped and T -colluding symmetric private information retrieval (SPIR). This is the first work to study SPIR with X-security in classical or quantum variations.
arXiv.org
Yalin E. Sagduyu, Tugba Erpek, Aylin Yener, Sennur Ulukus
This paper studies task-oriented, otherwise known as goal-oriented, communications, in a setting where a transmitter communicates with multiple receivers, each with its own task to complete on a dataset, e.g., images, available at the transmitter. A multi-task deep learning approach that involves training a common encoder at the transmitter and individual decoders at the receivers is presented for joint optimization of completing multiple tasks and communicating with multiple receivers. By providing efficient resource allocation at the edge of 6G networks, the proposed approach allows the communications system to adapt to varying channel conditions and achieves task-specific objectives while minimizing transmission overhead. Joint training of the encoder and decoders using multi-task learning captures shared information across tasks and optimizes the communication process accordingly. By leveraging the broadcast nature of wireless communications, multi-receiver task-oriented communications (MTOC) reduces the number of transmissions required to complete tasks at different receivers. Performance evaluation conducted on the MNIST, Fashion MNIST, and CIFAR-10 datasets (with image classification considered for different tasks) demonstrates the effectiveness of MTOC in terms of classification accuracy and resource utilization compared to single-task-oriented communication systems.
arXiv.org
Subhankar Banerjee, Priyanka Kaswan, Sennur Ulukus
"Timestomping" alters the timestamps of packets. Here, the authors consider a slotted communication system consisting of a source, a cache, a user and a timestomping adversary. There is an adversary in the system which completely controls the cache to user communication link. Whenever the user receives a cached update packet, the user compares the time stamp of the packet it has with the time stamp of the received packet, and keeps only the fresher packet while discarding the staler packet. The adversary can change the time stamp of the cached update packet, and by doing so, it can deceive the user by making it store a staler update packet with the cost of discarding a fresher update packet. The goal of the adversary is to increase the age of the user, while the goal of the source is to minimize the age of the user. The authors formulated this problem as an online learning problem and studied the competitive ratio for this problem. First, they proposed a deterministic algorithm and provided an upper bound on the competitive ratio for the proposed algorithm. Then, they proposed a universal lower bound for the studied system model. The extensions of the model with multiple users and/or multiple caches are interesting future directions.
arXiv.org
Arunabh Srivastava, Sennur Ulukus
This is the first work to show an age scaling result for a connectivity structure other than the ring and fully-connected networks that represent two extremes of network connectivity.
arXiv.org
Sajani Vithana, Sennur Ulukus
The goal of this work is to develop read-write schemes and storage mechanisms for FSL that efficiently utilize the available storage in each database to store the submodel parameters in such a way that the total communication cost is minimized while guaranteeing information- theoretic privacy of the updating submodel index and the values of the updates.
arXiv.org Also presented in part at IEEE ISIT 2022 and 2023
Sajani Vithana, Sennur Ulukus
Introduces the problem of deceptive information retrieval (DIR), in which a user wishes to download a required file out of multiple independent files stored in a system of databases while deceiving the databases by making the databases’ predictions on the user-required file index incorrect with high probability.
arXiv.org
Zhusheng Wang, Sennur Ulukus
The paper considers the federated submodel learning (FSL) problem in a distributed storage system. To resolve the issues of security and database repair, the authors propose a novel coding mechanism called "ramp secure regenerating coding" (RSRC), This mechanism stores the full model in a distributed manner.
arXiv.org
Subhankar Banerjee, Sennur Ulukus, Anthony Ephremides
The paper answers the question, "What is the optimal action for the BS when it receives a fresh update packet while an old update packet is being served; should the BS preempt the old packet and transmit the new packet with lower probability of successful transmission q1, or should it discard the new packet and continue to transmit the old packet with higher probability of successful transmission q2."
arXiv.org
Priyanka Kaswan, Sennur Ulukus
Considers a network of n user nodes that receives updates from a source and employs an age-based gossip protocol for faster dissemination of version updates to all nodes. The authors observe that very high or very low gossiping rates help curb misinformation, and misinformation spread is higher with moderate gossiping rates.
arXiv.org
Purbesh Mitra, Sennur Ulukus
Considers a fully-connected wireless gossip network which consists of a source and n receiver nodes. The source updates itself with a Poisson process and also sends updates to the nodes as Poisson arrivals. Upon receiving the updates, the nodes update their knowledge about the source. The nodes gossip the data among themselves in the form of Poisson arrivals to disperse their knowledge about the source. The total gossiping rate is bounded by a constraint. The goal of the network is to be as timely as possible with the source. The authors propose a scheme which they coin age sense updating multiple access in networks (ASUMAN), which is a distributed opportunistic gossiping scheme, where after each time the source updates itself, each node waits for a time proportional to its current age and broadcasts a signal to the other nodes of the network. This allows the nodes in the network which have higher age to remain silent and only the low-age nodes to gossip, thus utilizing a significant portion of the constrained total gossip rate.
arXiv.org and presentation at Allerton Conference 2022
Sajani Vithana, Zhusheng Wang, Sennur Ulukus
The authors provide an introduction to basic private information retrieval (PIR) with examples, followed by a brief description of its immediate variants. They then provide a detailed discussion on the conceptual extensions of PIR, along with potential research directions.
arXiv.org
Priyanka Kaswan, Sennur Ulukus
This work shows that connectivity improves resilience against jamming attacks and preserves timeliness of disseminated information; while the ring network (the lowest end of connectivity) is able to neutralize up to √n jammers, the fully connected network (the highest end of connectivity) is able to neutralize up to n log n jammers, in an n-user gossip network.
arXiv.org and presented in part at the Asilomar Conference, 2022
Sajani Vithana, Sennur Ulukus
In federated learning (FL), a machine learning (ML) model is collectively trained by a large number of users, using their private data in their local devices. With top r sparsification in FL, the users only upload the most significant r fraction of updates, and the servers only send the most significant r′ fraction of parameters to the users in order to reduce the communication cost. However, the values and the indices of the sparse updates leak information about the users’ private data. In this work, the authors consider an FL setting where N non-colluding databases store the model to be trained, from which the users download and update sparse parameters privately, without revealing the values of the updates or their indices to the databases. They propose four schemes with different properties to perform this task while achieving the minimum communication costs, and show that the information theoretic privacy of both values and positions of the sparse updates can be guaranteed. This is achieved at a considerable storage cost, though. To alleviate this, they generalize the schemes in such a way that the storage cost is reduced at the expense of a certain amount of information leakage, using a model segmentation mechanism. In general, they provide the tradeoff between communication cost, storage cost and information leakage in private FL with top r sparsification.
arXiv.org
Sajani Vithana, Sennur Ulukus
A look at the problem of private read update write (PRUW) with heterogeneous storage constrained databases in federated submodel learning (FSL).
arXiv.org
Priyanka Kaswan, Sennur Ulukus
This paper addresses a network consisting of n nodes that aim to track a continually updating process or event. To disseminate updates about the event to the network, two sources are available, such that information obtained from one source is considered more reliable than the other source. The nodes wish to have access to information about the event that is not only latest but also more reliable, and prefer a reliable packet over an unreliable packet even when the former is a bit outdated with respect to the latter. The authors study how such preference affects the fraction of users with reliable information in the network and their version age of information. They derive the analytical equations to characterize the two quantities, long-term expected fraction of nodes with reliable packets and their long-term expected version age using stochastic hybrid systems (SHS) modelling and study their properties.
arXiv.org
Priyanka Kaswan, Melih Bastopcu, Sennur Ulukus
Considers a system consisting of a server, which receives updates for N files according to independent Poisson processes.
IEEE Transactions on Wireless Communications
Zhusheng Wang, Sennur Ulukus
Considers the federated submodel learning (FSL) problem and proposes an approach where clients are able to update the central model information theoretically privately.
arXiv.org
Yalin E. Sagduyu, Sennur Ulukus, Aylin Yener
This paper studies the notion of age in task-oriented communications that aim to execute a task at a receiver utilizing the data at its transmitter.
arXiv.org
Subhankar Banerjee, Sennur Ulukus, Anthony Ephremides
This work considers a time slotted communication system consisting of a base station (BS) and a user. At each time slot an update packet arrives at the BS with probability p, and the BS successfully transmits the update packet with probability q over an erasure channel. The authors assume that the BS has a unit size buffer where it can store an update packet upon paying a storage cost c. There is a trade-off between the age of information and the storage cost. This trade-off is formulated as a Markov decision process and find an optimal switching type storage policy.
arXiv.org
Subhankar Banerjee, Sennur Ulukus, Anthony Ephremides
We consider a time slotted communication network consisting of a base station (BS), an adversary, N users and Ns communication channels. In the first part of the paper, we consider the setting where Ns communication channels Ns are heterogeneously divided among N users. The BS transmits an update to the ith user on a subset of the communication channels Ns,i where Ns,i ∩ Ns,j is not necessarily an empty set. At each time slot, the BS transmits an update packet to a user through a communication channel and the adversary aims to block the update packet sent by the BS by blocking a communication channel. The BS has n discrete transmission power levels to communicate with the users and the adversary has m discrete blocking power levels to block the communication channels. The probability of successful transmission of an update packet depends on these power levels. The BS and the adversary have a transmission and blocking average power constraint, respectively. We provide a universal lower bound for the average age of information for this communication network. We prove that the uniform user choosing policy, the uniform communication channel choosing policy with any arbitrary feasible transmission power choosing policy is 4 optimal; and the max-age user choosing policy, the uniform communication channel choosing policy with any arbitrary feasible transmission power choosing policy is 2 optimal. In the second part of the paper, we consider the setting where the BS chooses a transmission policy and the adversary chooses a blocking policy from the set of randomized stationary policies and Ns,i = Ns for all i, i.e., all users can receive updates on all channels. We show that a Nash equilibrium may or may not exist for this communication network, and identify special cases where a Nash equilibrium always exists.
arXiv.org
Priyanka Kaswan, Sennur Ulukus
Considers gossip networks consisting of a source that maintains the current version of a file, n nodes that use asynchronous gossip mechanisms to disseminate fresh information in the network, and an oblivious adversary who infects the packets at a target node through data timestamp manipulation, with the intent to replace circulation of fresh packets with outdated packets in the network. The authors demonstrate how network topology capacitates an adversary to influence age scaling in a network.
arXiv.org
Purbesh Mitra, Sennur Ulukus
Considers gossiping in a fully-connected wireless network consisting of n nodes. The network receives Poisson updates from a source, which generates new information. The nodes gossip their available information with the neighboring nodes to maintain network timeliness. The authors propose two gossiping schemes, one semi-distributed and the other one fully- distributed.
arXiv.org
2022
Matin Mortaheb, Sennur Ulukus
An algorithm that uses exchanged gradients to calculate the correlations among tasks automatically, and dynamically adjusts the communication graph to connect mutually beneficial tasks and isolate those that may negatively impact each other.
arXiv.org
Yalin E. Sagduyu, Tugba Erpek, Sennur Ulukus, and Aylin Yener
This paper highlights vulnerabilities of deep learning-driven semantic communications to backdoor (Trojan) attacks.
arXiv.org
Yalin E. Sagduyu, Tugba Erpek, Sennur Ulukus, and Aylin Yener
The authors model the transmitter-receiver functionalities as an autoencoder followed by a task classifier that evaluates the meaning of the information conveyed to the receiver.
arXiv.org
Sajani Vithana, Sennur Ulukus
In federated learning (FL) with top r sparsification, millions of users collectively train a machine learning (ML) model locally, using their personal data by only communicating the most significant r fraction of updates to reduce the communication cost. It has been shown that the values as well as the indices of these selected (sparse) updates leak information about the users’ personal data. In this work, we investigate different methods to carry out user-database communications in FL with top r sparsification efficiently, while guaranteeing information theoretic privacy of users’ personal data.
arXiv.org
Sajani Vithana, Sennur Ulukus
The authors investigate the trade-off between rate, privacy and storage in federated learning (FL) with top r sparsification, where the users and the servers in the FL system only share the most significant r and r′ fractions, respectively, of updates and parameters in the FL process, to reduce the communication cost.
arXiv.org
Yalin E. Sagduyu, Sennur Ulukus, Aylin Yener
Communications systems to date are primarily designed with the goal of reliable (error-free) transfer of digital sequences (bits). Next generation (NextG) communication systems are beginning to explore shifting this design paradigm of reliably decoding bits to reliably executing a given task. Task-oriented communications system design is likely to find impactful applications, for example, considering the relative importance of messages. In this paper, a wireless signal classification is considered as the task to be performed in the NextG Radio Access Network (RAN) for signal intelligence and spectrum awareness applications such as user equipment (UE) identification and authentication, and incumbent signal detection for spectrum co-existence.
arXiv.org
Cemil Vahapoglu, Matin Mortaheb, Sennur Ulukus
Multi-task learning (MTL) is a learning paradigm to learn multiple related tasks simultaneously with a single shared network where each task has a distinct personalized header network for fine-tuning. MTL can be integrated into a federated learning (FL) setting if tasks are distributed across clients and clients have a single shared network, leading to personalized federated learning (PFL). To cope with statistical heterogeneity in the federated setting across clients which can significantly degrade the learning performance, the authors use a distributed dynamic weighting approach.
arXiv.org
Mustafa Doger, Sennur Ulukus
The authors improve security-latency bounds of Nakamoto consensus by analyzing the race between adversarial and honest chains in three different phases: pre-mining, confirmation and post-confirmation.
arXiv.org
Zhusheng Wang, Sennur Ulukus
Considers the problem of symmetric private information retrieval (SPIR) with user-side common randomness.
IEEE Journal on Selected Areas in Information Theory
Brian Kim, Yalin E. Sagduyu, Kemal Davaslioglu, Tugba Erpek, Sennur Ulukus
This paper studies the privacy of wireless communications from an eavesdropper that employs a deep learning (DL) classifier to detect transmissions of interest.
Entropy
Matin Mortaheb, Cemil Vahapoglu, Sennur Ulukus
The authors develop FedGradNorm, a distributed dynamic weighting algorithm that balances learning speeds across tasks by normalizing the corresponding gradient norms in PF-MTL, and HOTA-FedGradNorm, which uses over-the-air aggregation (OTA) with FedGradNorm in a hierarchical FL (HFL) setting. HOTA-FedGradNorm is designed to have efficient communication between a parameter server (PS) and clients in the power- and bandwidth-limited regime. Both frameworks are capable of achieving a faster training performance compared to equal-weighting strategies, and compensate for imbalanced datasets across clients and adverse channel effects.
Algorithms
Sajani Vithana, Sennur Ulukus
An investigation of the problem of private read update write (PRUW) in relation to private federated submodel learning (FSL), where a machine learning model is divided into multiple submodels based on the different types of data used to train the model.
arXiv.org
Emre Ozfatura, Deniz Gündüz, Sennur Ulukus
Gradient descent methods are commonly employed in machine learning problems to optimize the parameters of the model in an iterative fashion. The authors propose a novel gradient coding scheme which allows multiple coded computations to be conveyed from each worker to the master per iteration. They numerically show that the proposed scheme with multi-message communication, together with clustering, provides significant improvements in the average completion time (of each iteration), with minimal or no increase in communication load.
arXiv.org
Sajani Vithana, Sennur Ulukus
The authors investigate the problem of private read update write (PRUW) in federated submodel learning (FSL) with sparsification.
arXiv.org
Batuhan Arasli, Sennur Ulukus
Considers a dynamic infection spread model based on the discrete SIR model which assumes infections to be spread over time via infected and non-isolated individuals. Introduces and studies a novel performance metric that can be used to measure how fast a given algorithm can control the spread of a disease. The authors introduce and characterize the performance of a novel dynamic SAFFRON based group testing algorithm.
arXiv.org
Zhusheng Wang, Sennur Ulukus
Following the concepts of gachapon as well as blind box, the authors introduce a digital blind box between a user and a server in a communication network. This is a new concept called random SPIR (RSPIR). In reference to the conventional SPIR, the only difference is that, in RSPIR there is no input at the user side. That is, the user does not send any queries to the databases, and ultimately receives a random message from the databases. This requirement is referred to as random reliability. Interestingly, the three requirements of RSPIR, namely, random reliability, database privacy and user privacy, strictly correspond to ththree characteristics of the digital blind box, making it equivalent to the RSPIR.
arXiv.org
Priyanka Kaswan, Sennur Ulukus
A study of the effects of timestomping attacks on the age of gossip in a large fully connected network.
arXiv.org
Priyanka Kaswan, Sennur Ulukus
The authors consider a system with a source that maintains the most current version of a file, and a ring network of n user nodes that wish to acquire the latest version of the file. The source gets updated with newer file versions as a point process, and forwards them to the user nodes, which further forward them to their neighbors using a memoryless gossip protocol. They then construct an alternate system model of mini-rings and prove that the version age of the original model can be sandwiched between constant multiples of the version age of the alternate model.
arXiv.org
Elza Erkip, Giuseppe Durisi, Robert Heath, Thomas Marzetta, Petar Popovski, Meixia Tao, Sennur Ulukus
The introductory editorial for a special issue exploring how new advances in information theory can impact future communication systems. Papers address issues at the heart of next generation wireless and wired networks<./p>
IEEE Journal on Selected Areas in Information Theory
Matin Mortheb, Cemil Vahapoglu, Sennur Ulukus
FedGradNorm uses a dynamic-weighting method to normalize gradient norms to balance learning speeds among different tasks. It improves the overall learning performance in a personalized federated learning setting.
arXiv.org
Mehlih Bastopcu, Sennur Ulukus
The researchers consider timely tracking of infection status of individuals in a population. For exponential infection and healing processes with given rates, they determined the rates of exponential testing processes. They considered errors on the test measurements and observed that in order to combat the test errors, a limited portion of the population may be tested with higher test rates. They observed in numerical results that the test rates depend on the individuals’ infection and healing rates, the individuals’ last known state of healthy or infected, as well as the health care provider’s priorities of detecting infected people versus detecting recovered people more quickly.
arXiv.org
Sajani Vithana, Sennur Ulukus
Investigates the problem of private federated submodel learning, where a machine learning model is divided into M submodels and stored in N databases, from which a given user privately reads, updates and writes back an arbitrary submodel.
IEEE International Conference on Communications 2022
Omur Ozel, Aylin Yener, Sennur Ulukus
In status update systems, multiple features carried by the status updating process require pursuit of objectives beyond timeliness measured by the age of information of updates. This paper consider such a problem where the transmitter sends status update messages through a noiseless binary energy harvesting channel that is equivalent to a timing channel. The transmitter aims to amplify or mask the energy state information that is carried in the updating process. The receiver extracts encoded information, infers the energy state sequence while maintaining timeliness of status updates. Consequently, the timings of the updates must be designed to control the message rate, the energy state uncertainty, and the age of information. The authors investigate this three-way trade-off between the achievable rate, the reduction in energy arrival state uncertainty, and the age of information, for zero and infinite battery cases.
arXiv.org
Subhankar Banerjee, Sennur Ulukus
The authors investigate the game theoretic equilibrium points of a status updating system with an adversary that jams the updates in the downlink. They consider the system models both with and without diversity.
arXiv.org
Subhankar Banerjee, Sennur Ulukus
Considers a communication system where a base station serves N users, one user at a time, over a wireless channel. The authors consider the timeliness of the communication of each user via the age of information metric. A constrained adversary can block at most a given fraction, α, of the time slots over a horizon of T slots, i.e., it can block at most αT slots. They show that an optimum adversary blocks αT consecutive time slots of a randomly selected user. The interesting consecutive property of the blocked time slots is due to the cumulative nature of the age metric.
arXiv.org
Sajani Vithana, Sennur Ulukus
Investigates the problem of private read update write (PRUW) in relation to federated submodel learning (FSL) with storage constrained databases.
arXiv.org
Zhusheng Wang, Sennur Ulukus
This work considers the total (upload plus download) communication cost of two-database symmetric private information retrieval (SPIR) through its relationship to conditional disclosure of secrets (CDS).
arXiv.org
Priyanka Kaswan, Sennur Ulukus
Presents a class of gossip protocols that achieve O(1) age at a typical node in a single-file system and O(n) age at a typical node for a given file in an n-file system. Shows that file slicing and network coding based protocols fall under the presented class of protocols.
arXiv.org
Batuhan Arasli, Sennur Ulukus
A study of a dynamic infection spread model, inspired by the discrete time SIR model, where infections are spread via non-isolated infected individuals.
arXiv.org
Mustafa Doger, Sennur Ulukus
The authors consider dynamical group testing problem with a community structure. With a discrete-time SIR (susceptible, infectious, recovered) model, we use Dorfman’s two-step group testing approach to identify infections, and step in whenever necessary to inhibit infection spread via quarantines.
arXiv.org
2021
Brian Kim, Tugba Erpek, Yalin E. Sagduyu, Sennur Ulukus
By moving from massive antennas to antenna surfaces for software-defined wireless systems, the reconfigurable intelligent surfaces (RISs) rely on arrays of unit cells to control the scattering and reflection profiles of signals, mitigating the propagation loss and multipath attenuation, and thereby improving the coverage and spectral efficiency. In this paper, covert communication is considered in the presence of the RIS.
arXiv.org
Bruno Clerck, Sennur Ulukus, Stark Draper, Salman Avestimehr, Osvaldo Simeone
Wireless power transfer (WPT) and wireless information and power transfer (WIPT) have received growing attention in the research community in the past few years. In this special issue, a total of fourteen papers present state-of-the-art results in the broad area of wireless transmission of information and power with a special emphasis on signal processing advances. The special issue starts with a guest editor-authored tutorial overview paper that reviews the signal processing, machine learning, sensing, and computing techniques, challenges and opportunities in future networks based on WPT and WIPT. The tutorial paper is then followed by thirteen technical papers.
IEEE Journal on Selected Topics in Signal Processing, special issue, Vol. 15, No. 5
Pulkit Grover, Viveck Cadambe, Sennur Ulukus, Stark Draper, Salman Avestimehr, Osvaldo Simeone
Computing is the next frontier for information theory. Intellectually, the goal of coded computing has been of interest from the days of von Neumann and Shannon. von Neumann examined this issue in his 1956 paper, “Probabilistic Logics and the Synthesis of Reliable Organisms from Unreliable Components,” which was in turn motivated intellectually by Shannon’s 1948 paper, and by the application of understanding reliability of seemingly noisy biological systems. While the original biological application remains ill-understood, the recent increasing use of decentralized and distributed computing architectures, as well as increasingly noisy technologies at a device level, have motivated a resurgence of interest in the problem. This special issue covers several areas within this problem space.
IEEE Journal on Selected Areas in Information Theory, special issue, Vol. 2, No. 3
Brian Kim, Yi Shi, Yalin E. Sagduyu, Tugba Erpek, Sennur Ulukus
A consideration of adversarial machine learning-based attacks on power allocation where the base station (BS) allocates its transmit power to multiple orthogonal subcarriers by using a deep neural network (DNN) to serve multiple user equipments (UEs).
arXiv.org
Mustafa Doger, Sennur Ulukus
The authors consider a zero-error probabilistic group testing problem where individuals are defective independently but not with identical probabilities, and propose a greedy set formation method to build sets of individuals to be tested together.
arXiv.org
Ahmed Arafa, Jing Yang, Sennur Ulukus, H. Vincent Poor
A status updating system is considered in which data from multiple sources are sampled by an energy harvesting sensor and transmitted to a remote destination through an erasure channel. The goal is to deliver status updates of all sources in a timely manner, such that the cumulative long-term average age-of-information (AoI) is minimized.
IEEE Transactions on Green Communications and Networking
Melih Bastopcu, Baturalp Buyukates, Sennur Ulukus
The authors consider the binary freshness metric for gossip networks that consist of a single source and n end-nodes, where the end-nodes are allowed to share their stored versions of the source information with the other nodes.
arXiv.org
Batuhan Arasli, Sennur Ulukus
A novel infection spread model based on a random connection graph which represents connections between n individuals is proposed. Infection spreads via connections between individuals and this results in a probabilistic cluster formation structure as well as a non-i.i.d. (correlated) infection status for individuals.
2021 IEEE International Symposium on Information Theory
Zhusheng Wang, Karim Banawan, Sennur Ulukus
Here, the authors consider the problem of multi-party private set intersection (MP-PSI).
2021 IEEE International Symposium on Information Theory
Sajani Vithana, Karim Banawan, Sennur Ulukus
Investigates the problem of semantic private information retrieval (PIR) from coded databases, where a user requires to download a message out of M independent messages, without revealing its identity to the databases.
2021 IEEE International Symposium on Information Theory
Karim Banawan, Ahmed Arafa, Sennur Ulukus
The authors introduce the problem of timely private information retrieval (PIR) from N non-colluding and replicated servers.
arXiv.org
Roy Yates, Yin Sun, D. Richard Brown III, Sanjit K. Kaul, Eytan Modiano, Sennur Ulukus
The authors are guest editors for a special issue on Age of Information of the IEEE Journal on Selected Areas in Communications. These editors have contributed a survey that introduces research in data freshness and provides a broad summary of recent work. The survey is followed by 20 contributed papers that reflect the state of the art in AoI research.
IEEE Journal on Selected Areas in Communications, special issue on Age of Information in real-time cyberphysical systems
Brian Kim, Yalin E. Sagduyu, Tugba Erpek, Sennur Ulukus
The authors present an adversarial attack by generating adversarial perturbations to manipulate over-the-air captured RSSs as input to the DNN. This attack reduces the IA performance significantly and fools the DNN into choosing beams with small RSSs compared to jamming attacks with Gaussian or uniform noise.
arXiv.org
Baturalp Buyukates, Melih Bastopcu, Sennur Ulukus
The authors use the version age metric to quantify information timeliness at receiver nodes. They consider disconnected, ring, and fully connected network topologies for each cluster.
arXiv.org
Zhusheng Wang, Sennur Ulukus
A look at the problem of symmetric private information retrieval (SPIR) with user-side common randomness.
arXiv.org
Priyanka Kaswan, Melih Bastopcu, Sennur Ulukus
The paper observes that freshness for a file increases with increase in consolidation of rates across caches. To solve the multi-cache problem, the authors first solve the auxiliary problem of a single-cache system. They then rework this auxiliary solution to a parallel-cache network by consolidating rates to single routes as much as possible. This yields an approximate (sub-optimal) solution for the original problem.
arXiv.org
Melih Bastopcu, Sennur Ulukus
The authors consider a cache updating system with a source, m caches and a user. They note that for a given set of update rates for the user (resp. for the caches), the optimal rate allocation policy for the caches (resp. for the user) is a threshold policy, where the optimal update rates for rapidly changing files at the source may be equal to zero.
Sennur Ulukus website
2020
Baturalp Buyukates, Sennur Ulukus
Considers a federated learning framework in which a parameter server trains a global model by using n clients without actually storing the client data centrally at a cloud server. Focusing on a setting where the client datasets are highly changing and temporal in nature, the authors investigate the timeliness of model updates and propose a novel timely communication scheme.
arXiv.org
Baturalp Buyukates, Sennur Ulukus
A study of the age performance of uncoded and coded (repetition coded, MDS coded, and multi-message MDS (MM-MDS) coded) schemes in the presence of stragglers under i.i.d. exponential transmission delays and i.i.d. shifted exponential computation times.
2020 Asilomar Conference on Signals, Systems and Computers
Baturalp Buyukates, Emre Ozfatura, Sennur Ulukus, and Deniz Gündüz
Proposes a novel gradient coding (GC) scheme that utilizes dynamic clustering, denoted by GC-DC, to speed up the gradient calculation.
arXiv.org
Zhusheng Wang, Karim Banawan, Sennur Ulukus
Proposes a novel achievable scheme for the MP-PSI problem. The scheme hinges on a careful design and sharing of randomness between client parties prior to commencing the MP-PSI operation.
arXiv.org
Melih Bastopcu, Sennur Ulukus
Considers a cache updating system with a source, a cache with limited storage capacity, and a user. Studies the tradeoff between storing files at the cahce and directly opbtining files from the source at the expense of additional transmission times.
arXiv.org
Sajani Vithana, Karim Banawan, Sennur Ulukus
The authors derive conditions for the semantic PIR capacity to exceed the classical PIR capacity with equal priors and sizes. Our results show that the semantic PIR capacity can be larger than the classical PIR capacity when longer messages have higher popularities.
ece.umd.edu
Roy D. Yates, Yin Sun, D. Richard Brown III, Sanjit K. Kaul, Eytan Modiano, Sennur Ulukus
A summary of recent contributions in the broad area of age of information (AoI).
arXiv.org
Brian Kim, Yalin E. Sagduyu, Tugba Erpek, Kemal Davaslioglu, Sennur Ulukus
From an adversarial machine learning perspective, the work shows how to use multiple antennas at the adversary to improve the adversarial (evasion) attack performance.
arXiv.org
Brian Kim, Yalin Sagduyu, Kemal Davaslioglu, Tugba Erpek, Sennur Ulukus
Demonstrates the feasibility of covert communications in a wireless communication system when a cooperative jammer designs its perturbation signal to fool an eavesdropper's DL-based classfier into classifying ongoing transmissions as noise.
arXiv.org
Zhusheng Wang, Karim Banawan, Sennur Ulukus
A study of the problem of private set intersection. Presents a novel capacity-achieving scheme that builds seamlessly over the multi-message private information retrieval scheme.
conference paper
Melih Bastopcu, Sennur Ulukus
For a cache updating system with a source, a cache, and a user, the authors provide an alternating maximization-based method to find update rates for the cache(s) and the user to maximize the freshness of files at the user.
arXiv.org
Brian Kim, Yalin E. Sagduyu, Kemal Davaslioglu, Tugba Erpek, Sennur Ulukus
Presents over-the-air adversarial attacks against deep learning-based modulation classifiers, accounting for realistic channel and broadcast transmission effects. A certified defense method using randomized smoothing is also included.
arXiv.org
Melih Bastopcu, Baturalp Buyukates, Sennur Ulukus
Proposes a selective encoding scheme for a status updating system in which an information source generates independent and identically distributed update packets based on an observed random variable X which takes n values based on a known pmf.
arXiv.org
Sajani Vithana, Karim Banawan, Sennur Ulukus
The paper proposes two achievable schemes for achieving semantic private information retrieval capacity.
arXiv.org
Baturalp Buyukates, Sennur Ulukus
This work looks at an information update system in which status update packets are generated by a sampler and sent to a monitor node through a server node. Two scenarios are considered: Gilbert-Elliot service times and i.i.d. interarrival times; and Gilbert-Elliot interarrival times and i.i.d. service times. The authors determined the average age at the monitor node for both scenarios and characterized the age-optimal state transition matrix for the underlying Markov chain with and without an average cost constraint on the operation of the system.
arXiv.org
Melih Bastopcu, Sennur Ulukus
This work considers an information updating system where a source produces updates as requested by a transmitter, and observes a tradeoff between the attained average age and the mutual information between the original and partial updates.
arXiv.org
Melih Bastopcu, Sennur Ulukus
This work addresses the problem of optimal operation of a resource-constrained sampler that wishes to track multiple independent counting processes in a way that is as up to date as possible.
arXiv.org
Melih Bastopcu, Baturalp Buyukates, Sennur Ulukus
The researchers consider a status updating system in which an information source generates independent and identically distributed update packets based on an observed random variable X which takes n values based on a known probability mass function (pmf). The proposed selective policy achieves a lower average age than encoding all the realizations and determine the age-optimal k values for arbitrary pmfs.
arXiv.org
Baturalp Buyukates, Melih Bastopcu, Sennur Ulukus
The authors consider two scenarios: when the empty symbol does not reset the age, and when the empty symbol resets the age. They find the time average age of information and the age-optimal real codeword lengths, including the codeword length for the empty symbol, for both of these scenarios. Through numerical evaluations for arbitrary pmfs, the authors show that this selective encoding policy yields a lower age at the receiver than encoding every realization, and find the corresponding age-optimal k values.
conference paper
Baturalp Buyukates, Alkan Soysal, Sennur Ulukus
A study of age of information in a multiple source-multiple destination setting with a focus on its scaling in large wireless networks.
ece.umd.edu
Zhusheng Wang, Karim Banawan, Sennur Ulukus
An information theoretic approach to the Private Set Intersection (PSI) problem shows that it can be successfully recast as a multi-message symmetric private information retrieval (MM-SPIR) problem with message size 1.
arXiv.org
2019
Melih Bastopcu, Sennur Ulukus
The authors design an information update system that strikes a desired balance between information quality and freshness by solving for the optimum update scheme subject to a desired distortion level.
arXiv.org
Baturalp Buyukates, Sennur Ulukus
Investigates the age performance of uncoded and coded computation distribution algorithms and shows that a minimum data set-coded task distribution scheme asymptotically outperforms uncoded and repetition coded schemes.
arXiv.org
Karim Banawan, Sennur Ulukus
Explores the secure degrees of freedom of three new channel models: broadcast channel with combating helper, interference channel with selfish users, and multiple-access wiretap channel with deviating users. The paper investigates various malicious interactions that arise in networks, including active adversaries, and proves that a deviating user can drive the secure degrees of freedom to zero. However, the remaining users can exploit the intentional jamming signals as cooperative jamming signals against the eavesdropper and achieve an optimum secure degrees of freedom.
Entropy
2023
Qiang Zhu, Chau-Wai Wong, Zachary Lazri, Mingliang Chen, Min Wu, Chang-Hong Fu
To gain a better understanding of the performance at the module level and facilitate future research in explainable learning and artificial intelligence (AI) in physiological monitoring, this paper conducts an in-depth comparative study at the module level for video-based pulse rate tracking algorithms; a special focus is placed on challenging fitness scenarios involving significant movement.
techRxiv.org
2022
Muhammed Zahid Ozturk, Chenshu Wu, Beibei Wang, Min Wu, K. J. Ray Liu
Microphone-based voice activity detection systems usually require hotword detection and cannot perform well under the presence of interference and noise. Users attending online meetings in noisy environments usually mute and unmute their microphones manually due to the limited performance of interference-resilient VAD. To automate voice detection in challenging environments without dictionary limitations, the authors explore beyond microphones and propose to use mmWave-based sensing, which is already available in many smart phones and IoT devices. Their preliminary experiments in multiple places with several users indicate that mmWave-based VAD can match and surpass the performance of an audio-based VAD in noisy conditions, while being robust against interference.
IASA '22: Proceedings of the 1st ACM International Workshop on Intelligent Acoustic Systems and Applications, July 2022
Min Wu, Zachary McBride Lazri, Qiang Zhu, Mingliang Chen, Quanzeng Wang
Infrared thermographs (IRTs, also called thermal cameras) have been used to remotely measure elevated body temperature (BT) and respiratory rate (RR) during infectious disease outbreaks, such as COVID-19. To facilitate the fast measurement of BT and RR using IRTs in densely populated venues, it is desirable to have IRT algorithms that can automatically identify the best facial locations in thermal images to extract these vital signs. This paper introduces a unique system that can detect inner canthi and outer nostril edges directly in thermal images in two phases.
IEEE Access
2021
Joshua Mathew, Xin Tian, Chau-Wai Wong, Sushant M. Ranadive, Min Wu
It is recommended to regularly monitor the blood oxygen level for precaution. This paper proposes a noncontact method for SpO2 monitoring using hand videos acquired by smartphones.
arXiv.org
Joshua Mathew, Xin Tian, Min Wu, Chau-Wai Wong
Blood oxygen saturation (SpO2) is an essential indicator of respiratory functionality. This paper proposes the first convolutional neural network-based noncontact SpO2 estimation scheme using smartphone cameras.
arXiv.org
Ravi Garg, Adi Hajj-Ahmad, Min Wu
Electric Network Frequency (ENF) is a signature of power distribution networks that can be captured by multimedia recordings made in areas where there is electrical activity. This work explores the unchartered application of ENF signal analysis for intra-grid location estimation of multimedia data. This first study conducts experiments on power ENF signals and provides encouraging results in that direction. ENF signals offer a strong potential to be used as a location-stamp for recordings.
techrXiv.org
2020
Min Wu
A variety of nearly invisible “micro-signals” have played important roles in media security and forensics. These noise-like micro-signals are ubiquitous and typically an order of magnitude lower in strength or scale than the dominant ones. They are traditionally removed or ignored as nuances outside the forensic domain. This talk discusses the recent research harnessing micro-signals to infer a person’s physiological conditions. One type of such signals is the subtle changes in facial skin color in accordance with the heartbeat. Video analysis of this repeating change provides a contact-free way to capture photo-plethysmogram (PPG). While heart rate can be tracked from videos of resting cases, it is challenging to do so for cases involving substantial motion, such as when a person is walking around, running on a treadmill, or driving on a bumpy road. It will be shown in this talk how the expertise with micro-signals from media forensics has enabled the exploration of new opportunities in physiological forensics and a broad range of applications.
Keynote Invited Talk at 8th ACM Workshop on Information Hiding and Multimedia Security June 22–24, 2020 (virtual conference)
Mingliang Chen, Min Wu
Introduces the notion of threshold invariant fairness, which enforces equitable performances across different groups independent of the decision threshold. The paper proposes to equalize the risk distributions among the groups via two approximation methods.
arXiv.org
Sai Deepika Regani, Beibei Wang, Min Wu, K. J. Ray Liu
Gesture recognition using wireless sensing opened a plethora of applications in the field of human-computer interaction. However, most existing works are not robust without requiring wearables or tedious training/calibration. WiGRep is a time reversal-based gesture recognition approach using Wi-Fi, which can recognize different gestures by counting the number of repeating gesture segments. Built upon the time reversal phenomenon in RF transmission, the Time Reversal Resonating Strength is used to detect repeating patterns in a gesture. A robust low-complexity algorithm is proposed to accommodate possible variations of gestures and indoor environments. WiGRep is calibration-free and location and environment independent.
2020 IEEE International Conference on Acoustics, Speech and Signal Processing (ICASSP)